Back in 2011 I looked at a cartel’s encrypted radio system in Mexico and wondered aloud…
The first question that jumps to mind, however, is how secure and well monitored a relay could be in the remote locations?
Recently I also wondered aloud about the U.S. unilateral withdrawal from Syria and Africa as opening the door to unregulated Russian military exports.
Now a recent conference on electronic warfare sheds light on what that may mean for countries expected to start using Russian deals to fill the vacuum left by America’s withdrawal:
In 2015, Pavlenko said that Russia had been able to engage in mass sabotage of Russian-made radios that Ukraine was using at the time by triggering some sort of kill switch, which he described as a “virus,” remotely.
This raises questions about what sort of failsafe devices Russia may be hiding inside the military equipment it sells to partners around the world, which could allow them to disable key features remotely if those countries were to turn on them for any reason. The tactic also appears to have had the secondary benefit of forcing Ukrainian forces to switch to much more vulnerable commercial radios and cellular networks, which the Russians then also relentlessly attacked.
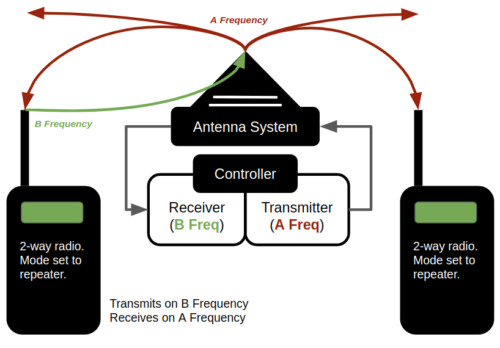
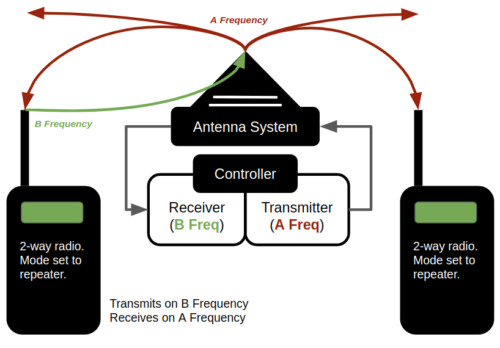
Nowhere has it been made clear what it means to say a virus or its kill-switch can be remotely activated on Russian-made radio repeaters, although it likely either intercepts traffic, blocks it or both.
Also I have not seen anyone mention that 2015 was 116 years after Emile Guarini Foresio invented the directed antenna for radio relay repeaters. The software controllers for repeaters may be new and laced with bugs, yet this radio architecture is fundamentally old technology.
Interesting to me now is a re-read of the 2016 story about a new military radio service launching in Ukraine:
Starting from March 1, 2016, Ukraine will have a radio service for the military, said Oleksiy Makukhin, an advisor to the Ukrainian defense minister. […] The creation of the radio station will be funded by Spirit of America, a United States charity based in California. […] The content will be transmitted via satellite in the FM-band.
It has been reported that satellites were not affected by any Russian attacks on radio communications in the Ukraine, and analysts attributed it to the fact Russia and Ukraine shared satellite services.
As soon as the U.S. started to withdraw from northern Syria the Russian equipment and troops started to deploy there under an agreement with Turkey.
However, the electronic warfare conference news report also mentions that sanctions against Russia have blocked key components and degraded the effectiveness and maintenance of their large inventory of electronic weaponry.
That suggests a threat today isn’t exactly what it was in 2015, unless Russia’s expanding market starts buying equipment from them with a new remote kill switch built-in despite sanctions.