NBC News just ran a story called The Vulnpocalypse about Anthropic’s decision to withhold its Mythos model from the public. The tone is, well, you know.
The author, Kevin Collier, lined up well-known cybersecurity vendors to stoke fear that AI-powered hackers will crash financial systems, lock up hospitals, and shut down water treatment plants.
Sigh.
Anyone who has worked in security long enough will recognize this FUD genre immediately. Replace “AI” with “war dialer” and this is the exact same article WarGames generated in 1983. At least back then we said the word war out loud instead of just implying it.
Captain Crunch Whistles for Everyone!
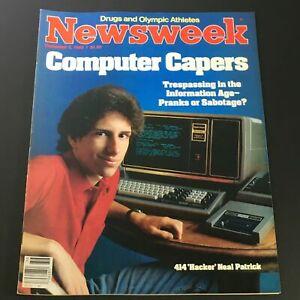
Back in 1983 some Milwaukee teenagers called the 414s (Milwaukee area code, yeah) waltzed into the unprotected computers at Los Alamos National Laboratory and Memorial Sloan-Kettering Cancer Center using nothing more exotic than a modem and a telephone line. The Newsweek cover on September 5, 1983 featured the word “hacker” for the first time on a major magazine cover.
Congress held hearings. Ronald Reagan was shown WarGames and asked the Joint Chiefs if the premise was real. Within a week the answer was: “Yes, the premise was technically possible.” Eighteen months later he pushed a signature onto NSDD-145, the first Presidential directive on computer security.
The actual legal consequences for the 414s were two years’ probation and a $500 fine for phone harassment. And even that seemed a bit much.
Neal Patrick became a media star. John Draper, Captain Crunch himself, had been phreaking the phone system with a cereal box whistle and people talked about it as though he were going to bring down AT&T. The whistle found in kids’ cereal boxes exploited in-band signaling on the analog phone network (2600 Hz tone on the same channel as voice). The fix was to push for the long-overdue move to out-of-band signaling (SS7). It stands as proof of the harm from natural monopolies refusing to invest in baseline safety. Dare I say history tends to rhyme even when it doesn’t repeat?
The vulnerability landscape was real, the exploitation was incremental, and the apocalyptic framing served the companies selling defenses. McAfee built an entire empire on this dynamic, most memorably during the 1992 Michelangelo virus panic, when John McAfee personally stoked fear that millions of computers would be destroyed on March 6th. The press amplified, the public panicked, almost nothing happened, and McAfee’s sales went through the roof. Perhaps most bizarre was how he became a security industry celebrity for undermining trust in the security industry. The vendors and conference attendees at events like BlackHat or Defcon acted as if Enron’s CEO should have been the toast of Wall Street.
The Same Article, Forty-Three Years Later
Collier’s piece follows the 1983 script with remarkable fidelity. The threat model is identical: hypothetical unsophisticated attackers gain access to powerful tools, critical infrastructure is vulnerable, and the proposed solution is withholding the tool from the public while sharing it with “partners.”
Imagine if some kids get a hold of sophisticated string and precision percussion instruments. Madness! Jazz? Rock and Roll? Catastrophe.
The sourcing follows the same pattern. Quote a government official convening emergency meetings (Treasury Secretary Bessent gathering the banks). Quote a vendor whose business model depends on threats expanding (Casey Ellis, founder of Bugcrowd). Quote a former FBI official warning about “wannabes” (Cynthia Kaiser, now a senior vice president at Halcyon). Close with water treatment plants. Everyone drinks water, it’s life. That’s a strong FUD move. Every quoted source in this piece stands to gain from security industry services related to the scariest story possible. Bugcrowd, Halcyon, Luta Security, Scythe. Who needs advertising when the article is the ad?
The Atlantic’s Priority
The Atlantic’s Matteo Wong went even further than Collier. His lede described Mythos as “a tool potentially capable of commandeering most computer servers in the world” that could “hack into banks, exfiltrate state secrets, and fry crucial infrastructure.”
It’s the opposite of reporting. It is the language of a film trailer. Anyone deep inside AI at the operations level knows how fundamentally flawed it remains versus humans.
Wong’s most consequential move was positioning Anthropic as a peer to nation-state intelligence services: “This level of cyberattack is typically available only to elite, state-sponsored hacking cells.” This framing matters because once the press treats a private company as operating at nation-state capability, the company inherits the presumption of nation-state authority over disclosure, access, and classification. Which is precisely what Project Glasswing establishes.
The Atlantic in 2023 published my co-authored article on real, documented AI harm. Tesla’s vehicles have been crashing into trees, killing motorcyclists, and veering off roads for years. The body count is in the hundreds now and the design flaws are landing in court cases. No Treasury Secretary convenes an emergency meeting over it. No consortium of tech giants receives $100 million to address it. 
But a company announces that its AI could hypothetically find software vulnerabilities faster than defenders could close them, and the entire press corps treats it like the fall of civilization.
Water Tanks
In 1915, a battle-hardened and war-weary Winston Churchill funded development of armored tractors meant to break through trenches, barbed wire, and machine gun nests. The British War Office ordered hundreds built under strict secrecy. The project was initially disguised as “water tanks”, which denied German intelligence any insight into what was actually being manufactured. The codename stuck, which is why ironically we still say tanks to speak of things that are not tanks.
The tank changed battlefield tactics, but it most certainly did not end battlefields. The immediate response was to dig better trenches and adapt doctrine. And, as always, a side that understood a new weapon’s limitations and integrated it into combined-arms operations won. A side that waxed about mythical wonder weapons, lost.
The history of the rifle tells the same story even more precisely. The bolt-action rifle gave way to the repeating rifle, which gave way to automatic fire. Each transition made a previous method more specialized. Each technology innovation demanded doctrinal adaptation. None of the innovations ended war. A rifle is not only still a rifle, the NRA whines constantly that you shouldn’t regulate an automatic rifle differently from a powder musket.
Vulnerability discovery has a similar question of progression. Manual research was bolt-action. Automated scanners were repeating. AI-assisted discovery is automatic. What Anthropic built with Mythos is a much faster fuzzer. And since they aren’t a security company at all, they probably are running around the office as if their hair is on fire yelling “what do we do, what do we do” instead of seeing it the way Churchill looked at a tank.
I say this from battle experience. When cloud computing arguably was first launched (e.g. Loudcloud, by Andreessen et al) I punched a massive hole right through claims about customer isolation. It was a normal finding, in my estimation. A service provider says customers are isolated, and my tool says nope. I handed the finding to the man sitting next to me and he literally jumped out of his chair, waved his hands in the air, ran out of the room and around the office yelling “OMG we’re in! We’re in!” He was, shall we say, less experienced.
Zero-day vulnerabilities have been found and disclosed continuously since the term was coined. Google’s Project Zero has been publishing them for a decade. The entire bug bounty industry exists because this is ordinary work. Finding 181 exploits faster than the previous tool found 2 is an efficiency gain in the rate of fire. It is not a civilizational rupture. And here is what the coverage systematically omits: faster discovery means faster patching. A tool that finds vulnerabilities at scale is, by definition, a tool that enables remediation at scale. That makes it a patch accelerator. The question is who controls the framing.
I have spent over a decade working with AI and showing companies both how to break and how to secure it. What I can report from being deep in the field for so long is that the fundamentals have not changed. You still need someone who knows where to point the weapon, and you still need a trench to fight from. The obfuscation is in calling the automatic rifle a magic alien death ray.
Withholding as the Product
“Our model is so dangerous we can’t release it” is, of course, the same sentence as “our model is so valuable you need us.” Such product mystique reads to me more like another geturked presentation to those in power than a proper public threat modeling disclosure.
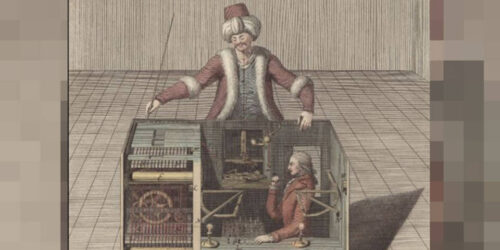
Rename “we built a better fuzzer” to “we possess a weapon too dangerous for the public” and you have a centuries-old trick in the defense contractor playbook.
Anthropic announced that Mythos produced 181 working exploits from a vulnerability set where the previous flagship model succeeded only twice. That is a real capability jump and should be taken seriously.
What should also be taken seriously is what happened next: Anthropic shared the model exclusively with twelve tech giants under Project Glasswing, backed by $100 million in usage credits. The withholding became the product launch. “Too dangerous to release” turned out to be the most effective marketing copy the industry has ever produced, and both Collier and Wong ran it as news.
The Treasury meeting completes a very shady picture. Bessent convenes the banks, Anthropic briefs the banks, and suddenly every major financial institution has a rather convenient public-private attachment to Anthropic’s vulnerability discovery capability. That is an undemocratic merger wrapped in false national security fearmongering.
Back Door
The timeline gives it away. On February 27, 2026, Defense Secretary Hegseth raged about making Anthropic a supply chain risk after the company refused his demands to strip safeguards against mass surveillance and autonomous weapons from Claude. Hegseth bloviated so hard, he made Anthropic the first American company ever given a designation normally reserved for foreign adversaries. Anthropic naturally sued, because common sense has to go to court. A judge blocked the designation.
Five weeks later, Anthropic announced Mythos and handed it directly to Microsoft, Google, Apple, Amazon, and the rest of the companies the Pentagon depends on for its entire technology stack. The front door closed and the back door opened wider. When the Secretary of Defense designates you a foreign adversary over a contract dispute, the direct route to military integration is blocked. But you can achieve the same position by making yourself the security backbone of every company the military depends on. No contract. No congressional testimony. No use restrictions. The money flows through the same channels. The brand stays “clean” of Hegseth.
The Doctrine, Not the Weapon
Grant and Sherman won the Civil War by combining coordinated force with the systematic destruction of the enemy’s capacity to produce war. The engagement mattered less than the doctrine. AI vulnerability discovery tools follow the same logic: they are force multipliers for whatever doctrine you already have. If your doctrine is “sell fear,” they push a LOT of fear. If your doctrine is “map the attack surface and hold the line,” they multiply that.
The question nobody in the Vulnpocalypse coverage has asked is whether zero-day resolution is now accelerating faster than zero-day discovery. If it is, then Mythos is a net defensive tool and the entire panic narrative collapses. Anthropic has the data to answer this. They have not published it, to my knowledge. My guess is they lack the security experience to frame it that way.
The 1983 version of this panic produced NSDD-145 and eventually the Computer Fraud and Abuse Act, real legislation born from manufactured urgency. The 2026 version is producing something structurally different: a private company functioning as a classification authority that decides who gets access to vulnerability discovery capabilities and on what terms. That is a larger institutional shift than the old Presidential directive, and it is happening while the press runs “Vulnpocalypse” headlines and quotes panic pill vendors.
The exhausted CISOs and security teams I talk to many times every day already know the AI tools are real and they know the rate of fire has changed. What they need is a defensible position against the flood of AI vendors who confuse a product launch with the end of the world.
Anthropic calls its patch accelerator Mythos for the same reason Churchill called his tractors tanks. The name disguises the use, preventing doctrinal analysis.
Churchill hid the function so the enemy couldn’t develop counterdoctrine. Anthropic hides the function so the market can’t judge how a defensive tool is being pitched as an offensive threat.


