People often incorrectly brand Luddites. The followers of a man named Ludd were very much in favor of proper and skilled (ethical) use of technology. But that’s not often what people mean when they invoke the Luddites.
Luddite advocacy was undermined by fraudulent counter-claims (those opposed tried to frame any ethical regulation of technology at all as an outright ban on use)… which resulted in armed aggression by private and government forces.
So why exactly were Luddites protesting for safety in technology and why were they shamelessly murdered for it?
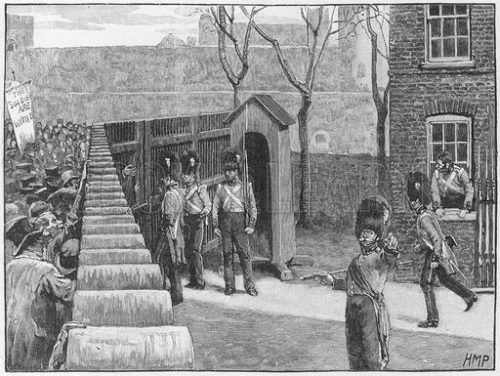
On this day in 1812 a group of a hundred or more (some say thousands) Luddites near Manchester attempted to enter Burton’s Mill as a peaceful protest. Armed guards of the mill as well as British soldiers fired live rounds into the crowd, killing up to a dozen people.
Hopefully someday soon this unfair chapter in history will stand corrected, and the Luddites’ cause cleared.
It’s still a very common misnomer and easy to find people unfortunately saying Luddites were opposed to technology.
They were not.
Sites like the Smithsonian have tried to clarify, yet obviously more still needs to be said.
The label now has many meanings, but when the group protested 200 years ago, technology wasn’t really the enemy.
Technology was not the enemy of Luddites!
Perhaps it helps if I put it like this. To say Luddites were anti-technology is like saying Robin Hood was anti-technology. Could anyone say “Robin Hood really hated the bow and arrow”?
No. That makes no sense, yet Robin Hood in fact has a lot in common with the Luddites. His story was about a moralist’s use of bow and arrow (use of disruptive technology in his day towards victory, as proven in the 1415 Battle of Agincourt).

Similarly to the legend of Robin Hood, a populist character of Ned Ludd rose out of the exact same Sherwood forest area of Nottingham. He also represented the fight for morality in the use of technology; Luddites demanded quality and expertise to be valued in technology above exploitation.
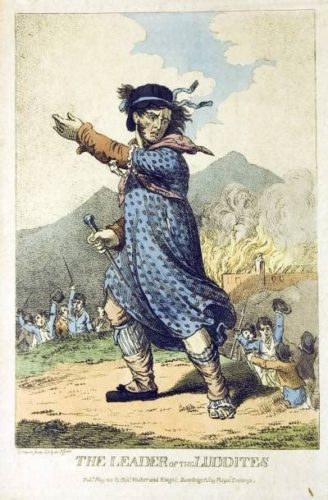
The Luddites therefore were latter day Robin Hood adherents, experts at technology who disliked machinery owners doing things known to increase the death and suffering of a worker.
The Wailers famously wrote a more modern lament into their 1970s lyrics as:
Today they say that we are free
Only to be chained in poverty
Good God, I think it’s illiteracy
It’s only a machine that make money.
In some sense, you might say these protests made them hackers of their day, experts at machines while at the same time protesting misuse.
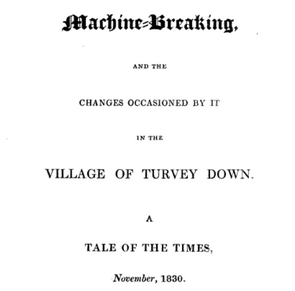
Texts were written about “machine breaking” that emphasized the need for improving safety and quality…
Now think about their opposition. The heavily armed mill owners in 1800s, targeted by Luddites, were like the Sheriff of Sherwood Forrest only 400 years later.
I find some people in tech at first glance don’t want to be associated with Luddites. Yet in actual fact who really wants to associate instead with a Sheriff in Robin Hood’s time let alone four centuries afterward, let alone today?

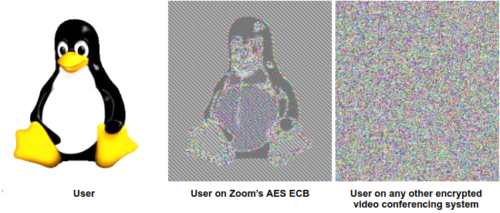
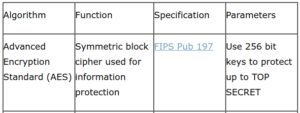
That is to say, in today’s terms, people in technology roles protesting immoral practices (e.g. the industrial dumpster fires of Zoom or Tesla) are… like the Luddites. Those (including myself) who have been calling for Zoom usage to be ended immediately are not rejecting technology — we’re holding it to a higher bar!
Luddites thus today would be the technical champions calling for and end to Zoom’s obviously deceitful and harmful business practices, and calling for technology made safer for everyone.
Those who have been taught that Luddites didn’t like technology thus have been misled; the entire point of the group was to righteously protest against immoral use of technology (wielded selfishly by owners towards obvious harms).
Even more tragically, people often leave out the fact that Luddites were ruthlessly murdered by factory gunmen and hanged for daring to defend society under a concept of greater good.
In truth, they inflicted less violence than they encountered. In one of the bloodiest incidents, in April 1812, some 2,000 protesters mobbed a mill near Manchester. The owner ordered his men to fire into the crowd, killing at least 3 and wounding 18. Soldiers killed at least 5 more the next day.
Earlier that month, a crowd of about 150 protesters had exchanged gunfire with the defenders of a mill in Yorkshire, and two Luddites died. Soon, Luddites there retaliated by killing a mill owner, who in the thick of the protests had supposedly boasted that he would ride up to his britches in Luddite blood. Three Luddites were hanged for the murder; other courts, often under political pressure, sent many more to the gallows or to exile in Australia before the last such disturbance, in 1816.
At least 8 killed in just one protest. Some estimates are double. But in all cases the government was using overwhelming force.
To be fair, Luddites reportedly also did commit violent acts against people, even though it ran counter their overall goals of social good.
Some claims were made that Luddites intimidated local populations into sheltering and feeding them, similar to charges against Robin Hood. That seems like dubious government propaganda, however, as Luddites were a populist movement and “melting away” was again a sign of popular support rather than violent intimidation tactics.
Indeed, more often there were accounts of Luddites sneaking into factories at night and cleverly taking soldiers’ guns away to destroy only the machines as a form of protest. People were set free and unharmed.
An exception was in the case above where a mill owner “boasted” of murdering Luddites and was arming guards and calling in the military… escalation unfortunately was set on a path where Luddites stepped up their defense/retaliation.
Don’t forget 1812 was a very violent time overall for the British, with tensions rising around inequality (food shortages) and protracted European war (1803–1815), including rising tangles with America over its relations with France.
Prime Minister Spencer Perceval, who extremely opposed the Luddites, was assassinated May 11, 1812 by a merchant named John Bellingham.
Bellingham walked up and shot Perceval point-blank, then calmly sat down on a bench nearby to wait his arrest. Conspiracy theories soon circled, suggesting American merchants and British banks were conspiring to end trade blockades with France.
A month after the May assassination was when the War of 1812 began with America.
All that being said, if you want to ensure technology improves, and doesn’t just exploit unsuspecting consumers to benefit a privileged few, read more about the populist Luddite as well as Robin Hood stories from Nottingham.
These legends represent disadvantaged groups appealing for justice against a tyranny of elites.
Also, consider how “General Ludd” was another (science) fiction about the Sherwood Forest by design.
Here’s a quick Ludd rhyme that was turned into a ticket to entry for meetings.
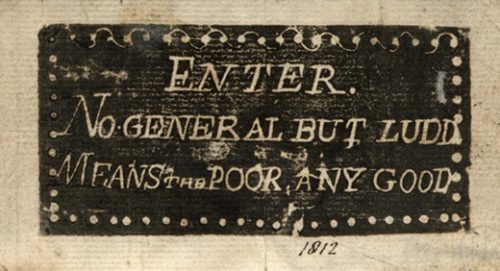
It was his (and Robin Hood’s) inauthenticity, as a face of the very real populist cause that made them impossible to kill.
On a remote yet related note, the “Jayhawk” was a mythical Irish bird that became the mascot of abolitionist militias in Kansas (and today is still the mascot of Kansas University)
The legend of Ludd kept “his” cause of justice alive despite overwhelming oppositional military forces. Allegedly British authorities invoked “posse comitatus” (it’s a thing Sheriffs are known to do) and deployed more military soldiers domestically to stop Luddites than during war with Napoleon.
Nottingham took on the appearance of a wartime garrison… authorities estimated the number of rioters at 3,000, but at any one time, no more than 30 would gather…
In American history we have similar heroes, such as the inauthentic yet also real General Tubman. She fought plantation owners in the same sense that Ludd fought mill owners; targeting the immoral use of machinery. The cotton engine (cotton ‘gin) was a machine invented to end slavery (by Catherine Greene), yet its IP was stolen and turned into a reason to expand and perpetuate slavery.
Surely slave owners would have called Tubman an anti-technology radical at war with their manufacturing if they could have made such absurd accusations stick (instead of her being remembered rightly as an American patriot, veteran, abolitionist and human rights champion).