Cloudflare kicked off Agents Week with a blog post asking important questions about AI infrastructure: “which agent are you, who authorized you, and what are you allowed to do?”
Then they moved on to talk about isolates.
The Right Stuff
The Cloudflare post core argument is that containers were built for one application to serve many users.
Of course they were. The efficiency of a “service” being multi-user is as old as humanity itself. We don’t ride the shared infrastructure of the Internet, enjoying the massive speed and efficiency gains, wishing we had laid our own dedicated fiber from every person we want to communicate with securely. History shows why. 
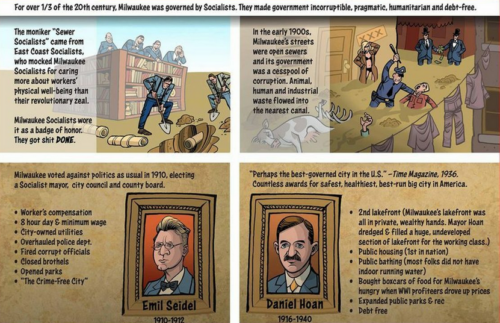
The dozens of CISOs I met with last week were asking me how do we run more agents? And I certainly was not telling them to light up one user, one agent, one task. To put it another way, if a CISO asks me about how to scale hardware, I might say let’s talk about a hypervisor to run software-based virtual machines. If a CISO asked me how to scale software-based machines, I might say let’s talk about containers… and so the logic of “sewer socialism” in shared infrastructure lives on.
Cloudflare enters this context saying containers now are too heavy for agents. V8 isolates start in milliseconds, use megabytes instead of gigabytes, and cost orders of magnitude less per session. At the scale agents require, isolates win.
This is correct. Cloudflare is stating the obvious. They have the network. They have the edge. They are like the contractors who provide the cafeteria for your office. But a cafeteria is not a chef. And a chef operating in your building, reading all your email, accessing all your financial accounts, and talking to your coworkers, in fact needs more than a fast startup time to serve hot meals on time.
The Wrong Stuff
Cloudflare’s post reveals a gap, yet they aren’t talking about it directly. Today’s agent deployments are “fraught with risk: prompt injection, data exfiltration, unauthorized API access, opaque tool usage.”
CISOs feel huge pressure to open up “productivity” gains yet can’t sign off because a security model doesn’t exist yet. OpenClaw is one of the biggest design disasters in software history: a single golden key that doesn’t rotate and can be stolen without detection.
Cloudflare’s answer is to merge their developer platform with their zero trust platform. Two products, built for different audiences, being stitched together like a Frankenstein. That takes time. And, for those who forget the science-fiction warning, stitching is not the same as weaving.
The artificially over-hyped open-source agent platform, one that suddenly showed up with 341,000 GitHub stars and little evidence for why, consolidates access to every messaging channel behind a single static token in a single process. No channel isolation. No credential rotation. No audit trail. It’s an embarrassment to the word engineering, a complete absence of design and no sense of accountability.
Cloudflare is stepping in where they operate, at the infrastructure layer. The compute, the network, the edge. And then what sits between that infrastructure and the user’s actual data remains an open question.
That question has an easy answer.
Are Your Agents Wirken Yet?
Wirken is a secure, model-agnostic AI agent orchestration platform. It exists because the tools that run agents against your messaging channels and business data should be built to deserve that access.
The security is not slopped in or bolted on. It is designed with baselines in mind and enforced at compile time.
Every channel adapter runs in its own OS process. A Slack credential cannot touch a Telegram session. This is not a runtime permission check that can be bypassed. It is a Rust phantom type constraint. Cross-channel access is a compiler error. It does not run. It does not build.
Credentials live in an encrypted vault using XChaCha20-Poly1305 with OS keychain integration. They are scoped per channel and rotate. The secret type has no Display, no Debug, no Serialize, no Clone. It zeroes on drop. A credential cannot leak through logging, serialization, or accidental copy because the type system will not allow it.
Every agent action is recorded in an append-only, SHA-256 hash-chained audit log before execution. Tamper with any entry and the chain breaks. Forward it to your SIEM. Hand it to your auditor. It is a complete, verifiable record of what every agent did, when, and with whose authorization.
Skills are signed with Ed25519. Unsigned code does not run. The skill registry is not a marketplace where 20% of entries are malicious. It is a supply chain with cryptographic verification.
The Cafeteria and the Chef
Cloudflare used a good analogy. A traditional application is like an industrial form of restaurant: fixed menu, optimized kitchen, high volume. An agent is a chef who asks what you want (chicken or shrimp), then improvises with whatever tools and ingredients the task requires.
Extend the analogy. The chef is in your office. You hand the chef keys to the entire building. The chef can open all your files, read all your communications, and assume your identity to send messages as you.
You want that chef to be fast with the meal. You also want to know which chef is in your building, who sent them, what they are allowed to touch, and a tamper-proof record of everything they did while they were there.
Cloudflare is building the high-speed kitchen. Fast counters, efficient burners, millisecond cleanup. Wirken is the system that makes sure that any chef you interact with is doing what that chef was authenticated and authorized to do. Different layers. Complementary.
What This Looks Like in Practice
Wirken ships as a single static Rust binary. No runtime dependencies. No Node.js. No container orchestrator. Install it, configure your channels and your model, and run it.
It is model-agnostic. Point it at Anthropic, Gemini, OpenAI, Ollama for local inference, or even Privatemode for confidential inference inside hardware enclaves. The orchestration layer does not care which model you use. The security guarantees are the same regardless.
It runs behind Cloudflare Tunnel today. Any self-hosted Wirken instance gets a public endpoint for webhook-based channel adapters without exposing ports. Cloudflare handles the network. Wirken handles the trust boundary.
It has nine channel adapters for a reference architecture: Telegram, Discord, Slack, Teams, Matrix, WhatsApp, Signal, Google Chat, iMessage. It comes with fifteen bundled skills (natively compatible with OpenClaw) and MCP server support.
Two Layers, One Stack
The shift to agents needs defense-in-depth. The compute layer that makes agents affordable at scale is coming faster than ever. Now an orchestration layer that makes agents safe to deploy is on the table.
Cloudflare asked great questions. Which agent are you, who authorized you, and what are you allowed to do?
The answer is here: github.com/gebruder/wirken
