Although I spent many months deep in the archives of British history to write my Master’s thesis on the WWII liberation of Ethiopia I continue to find things now that I wish I had known a long time ago.
 Lately I’ve been reading again about Mission 101, where just a few thousand men in an Allied expeditionary force were sent into Ethiopia to defeat a far greater Italian occupation force at least 10 times their size. It’s mentioned in books like “Fire in the night : Wingate of Burma, Ethiopia, and Zion,” or the more obvious title of…wait for it… “Mission 101”.
Lately I’ve been reading again about Mission 101, where just a few thousand men in an Allied expeditionary force were sent into Ethiopia to defeat a far greater Italian occupation force at least 10 times their size. It’s mentioned in books like “Fire in the night : Wingate of Burma, Ethiopia, and Zion,” or the more obvious title of…wait for it… “Mission 101”.
In late 1940 a group of five young Australian soldiers set out on a secret mission. Leading a small force of Ethiopian freedom fighters on an epic trek across the harsh African bush from the Sudan, the small incursion force entered Italian-occupied Ethiopia and began waging a guerilla war against the 250,000-strong Italian army. One of these men, Ken Burke, was Duncan McNab’s uncle.
The mission wasn’t actually about five Aussies, and I’ll get to that in a minute. The name seemed strange to me, in modern context, because we use 101 to imply some kind of basic level. Someone saying “Mission 101” today sounds almost exactly opposite to the task of taking a few soldiers into unknown territory against massive odds. That sounds really hard, right?
Top-ranked answer on a search engine is a Slate post called “101 101” that tells us the expression since the 1930s has meant a starter course for beginning students:
Many freshmen will kick off their college careers with courses like Psychology 101, English 101, or History 101. When did introductory classes get their special number? In the late 1920s. The Oxford English Dictionary finds the first use of “101” as an introductory course number in a 1929 University of Buffalo course catalog. Colleges and universities began to switch to a three-digit course-numbering system around this time.
This is a wholly unsatisfying answer. It takes for granted that in transition to a three number system someone would only use 101, and not 100, 010, 001, 000 or any other possible combinations.
Why 101?
I needed more. And the search engines were doing little to help, not least of all because searching for anything + “101” gives you an introduction to that topic and not the expression.
Instead I dug into the details within “Fire in the Night” by John Bierman and Colin Smith.
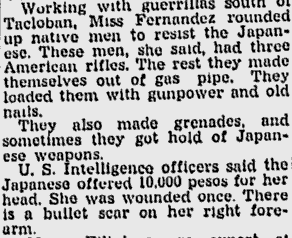
It says Mission 101 had a leader named Lt Col Daniel Sandford who served as artillery during WWI, and then as British Consul to Abyssinia before retiring there at the end of his term in office.
The key to this story, I soon figured out, is that WWI British artillery commonly used a fuse numbered 101 for their large explosive shells. The next question was why Sandford would transpose an old artillery fuse number on a WWI explosive shell to the WWII mission he ran?
This is where the story gets interesting.
After Italy invaded Ethiopia in October 1935 Sandford was forced to escape back to England. Italy then was poised to threaten British control of the Red Sea routes to Asia. The Sudan (occupied by Britain since 1899), bordering west Ethiopia, was thus directed by the British military to begin training Ethiopians as guerrilla forces ready to retake their country.
When Archibald Wavell was appointed General Officer Commanding-in-Chief in 1939 of Middle East Command over the Mediterranean and Middle East, he set about the task of asserting control over Red Sea routes as well as protecting Egypt (occupied by Britain since 1882, “sovereign” under Anglo-Egyptian Treaty of 1936). Wavell thus came up with a covert plan to encourage indigenous rebellion in Gojjam, a western Ethiopia province bordering Sudan where Italians had failed to establish control.
Guess what the name of that plan was.
October 1939 Britain estimated war with Italy was fast approaching and Sanford was dispatched back to Khartoum to gather Sudanese troops and Ethiopian exiles, arrange military supplies, and start heading east with his few thousand men. “Mission 101” was the plan to use a trigger group to detonate a larger popular uprising inside Ethiopia that would push the Italians out.
Mission 101 thus meant a small force of Ethiopians, Sudanese and Eritreans to rout the very large presence of Italian occupiers.
Embed from Getty Images
As a footnote, and as I’ve written about here before, Bletchley Park allegedly had cracked Italian Enigma encryption as early as 1936 giving a decisive advantage to the small force deployment in Mission 101.
Batey, who was only 19 at the time, cracked the code in an Italian Naval Enigma machine…
Australians don’t get a lot of mention in any of this, if any at all, despite by some accounts being tasked to help oversee the “Ethiopian patriot” forces.
The Americans in 1942, emulating/collaborating with the British, launched their own secretive Detachment 101:
The unit, officially designated as OSS Detachment 101, consisting initially of 21 members, began an intensive training program in early April 1942. William A. Peers, who later succeeded Eifler as commander of Detachment 101, said in his memoirs that the designation for the group was chosen to give the impression that the unit was well established and had been activated for a considerable length of time.
Clearly either Peers missed the Sandford memo or he intentionally created a fake “well established” backstory instead. It became a foundation that led to “the tenth group” of special forces in 1950s named to make the Soviets think there are at least nine others just like it.
Fascinating to think that 101 could have shifted from British military meaning the earliest and smallest step of a series to the American military meaning the opposite: a later stage and evidence of large impact. Although the OSS Detachment 101 in Burma was thought to be America’s “most effective tactical combat force”, to this day I don’t know of anyone who says 101 to suggest they had 100 priors.
There you have it. Given a history of British artillery fuse numbering, and the leadership role of WWI-veteran Sandford, the use of a small tactical action to trigger or initiate a much larger strategic impact makes sense as the origin of 101.
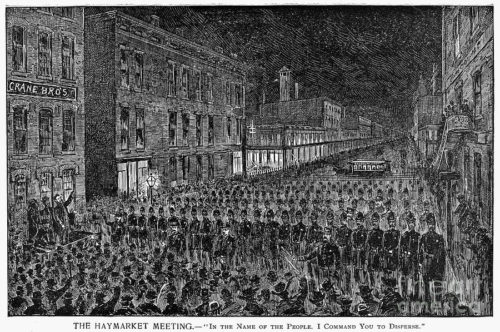
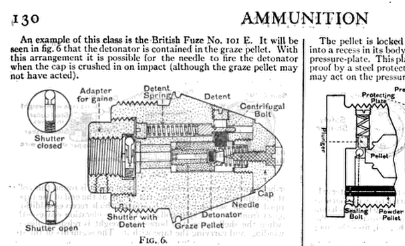
The best evidence of the exact number used on a fuse comes from a war museum file (IWM MUN 2582) which helps confirm that saying 101 went from military use to public in 1920s; set the stage as a common way to “starting” or “initiating”.

The No 101 percussion fuze was introduced in 1916 and represented an attempt to overcome the No 100 fuze’s weak points. The 101 did away with the ‘cocked pellet’, used a fixed needle, and placed the detonator in the graze pellet. The needle was originally pressed in, but loose needles often caused premature explosions and a screwed-in needle was used after the Mark I. The 101 ran to five ‘Marks’ and was declared obsolete in 1921.
A good example of public usage and general knowledge comes from the Encyclopedia Britannica of 1922, which explained in detail on page 130, that the 101 is an example of the graze fuze for artillery shells.
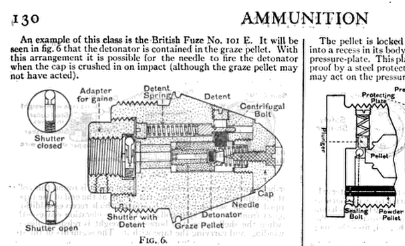
It ironically even uses the phrase “this class” to describe something other than what we would think of today when hearing about the 101 class becoming common in the 1930s.