The Electronic Frontier Foundation announced yesterday that it is leaving Twitter (rebranded X) after nearly twenty years on the platform. The stated reason: their engagement numbers have collapsed. Their blog post complains a single “Xcrement” now delivers less than 3% of what a Tweet reached before the rebranding. This is an attempt to claim it’s a matter of math, the platform numbers don’t add up.
However, EFF history is worth cross-referencing with this seemingly simple complaint. Something’s not right. EFF used to do real work. Bernstein v. DOJ made the encrypted internet possible. That history is exactly what makes their “Xodus” and current trajectory unforgivable.
An Interregnum
Two weeks ago, EFF announced that Nicole Ozer would be its new executive director, effective June 1. She sits on a state privacy regulatory board in January, then takes the helm of the organization that lobbies on privacy in March. That alone raises a conflict of interest question someone should be asking. Is that me?
Outgoing director Cindy Cohn has been on an outspoken national book tour for her memoir Privacy’s Defender, doing stops at City Lights, The Daily Show with Jon Stewart, Brooklyn Public Library with Anil Dash, and multiple events in DC and New York. She appears desperate for attention, pumping herself as the solo star of an organization that purports to represent the interests of many. The EFF homepage currently reads like it’s nothing more than a publicist’s landing page for her and her book, positioned high above the organization’s advocacy work.
On The Daily Show, the wheels fell off. Jon Stewart, one of the sharpest interviewers in the world, pressed Cohn on platform liability and algorithmic harm. He correctly called out social media as “algorithmically driven speech” and “monetized, incentivized, algorithmic clusterfuck.” That’s a fact. Cohn replied by going on an offensive attack, trying to discredit Stewart personally on his own show to divert attention from his question: comparing Facebook’s algorithm to Stewart choosing guests for his show. This unfounded, illogical, assault on Stewart didn’t do the EFF any favors.
Stewart raised environmental regulation as a model for platform harm. Cohn called protecting the environment a form of censorship. Pollution is a both sides argument now? Stewart pushed on liability. Cohn said people should never fight, just “leave” if they don’t like something. She said go to Bluesky, as if doubling down from false “both sides” of pollution to false “equivalence” of every technology is her big move. Stewart: “But if I shift over to Bluesky, then the world no longer makes sense.” Every structural solution Stewart raised, Cohn reframed with a hollow label of “censorship”. Don’t regulate, just leave.
The lady in first class is telling the other passengers to jump out the door while she stays. The person advocating departure keeps their posh seat.
Cohn also said, without irony, that she wishes a comprehensive privacy law would pass. A regulation like a comprehensive, top-down law without liability, without a regulator, without consequences is like her saying we should write a letter to Santa. Just keep giving more money to the EFF and she says your Santa may someday come. The fantasy of “comprehensive privacy law” is a cover for “just leave” as her daily operational reality.
Her carefully scripted and performed formulation was revealing, and deserves much more scrutiny.
Libertarianism, whatever good or bad we say about it, has an actual philosophical core: rights are inherent and worth defending where you stand. I’ll say it again. Foundational to libertarians is the fight, to engage in conflict, to make trouble. They don’t just run.
Locke. Mill. Hello?
The cypherpunks built PGP, Tor, encrypted communications because they believed in fighting for the space they occupied. John Gilmore, EFF’s own co-founder, said “The Net interprets censorship as damage and routes around it.” That is resistance, not departure. You don’t leave. You build tools. You encrypt. You stand your ground because you inherit a system of rights that enable your stand.
“Just leave” expressed by Cohn is an entirely different philosophy. It tells a victim to relocate rather than requiring the powerful actor to change. It abandons the space to whoever controls it. The burden falls on the displaced, not the aggressor. When Stewart raised environmental regulation as a model, Cohn rejected the rights of those who lose their environment. When he raised platform liability, she rejected the rights of those who lose their environment. Her only affirmative proposal: go somewhere else, as if somewhere else even exists. Your rights are portable, but only if you vacate the spaces where representation was supposed to exist. And when do you stop vacating?
Cohn used logic of every forced displacement in history.
The people who don’t belong should find somewhere they do. The space belongs to whoever holds power. Before extermination came emigration plans. Before the camps came “just leave.” Telling victims of algorithmic harm to abandon the platforms where their communities, businesses, and organizing infrastructure exist, rather than demanding those platforms be accountable, is capitulation dressed as choice. It serves the platform. It serves the advertiser. It does not serve the person. It is a centralization of power argument that pushes for individuals to lose rights, the literal negation of libertarian thought.
She went on a comedy show to sell a memoir and delivered a sermon on capitulation to a host who understood the problem far better than she did.
Cohn exposed herself, revealing something very problematic with accountability and the EFF itself.
The X departure lands in the gap between Cohn’s effective departure and Ozer’s arrival. The byline belongs to EFF’s social media manager, Kenyatta Thomas. Nobody with executive authority has to own the decision. Cohn is on tour. Ozer hasn’t started. A politically charged move authored during a leadership vacuum, by staff who can’t be held accountable at the executive level.
Let’s dig in.
Indulgences
EFF says it can’t stay on X because Musk fired the human rights team and failed to deliver transparent content moderation. But EFF will stay on Facebook, Instagram, TikTok, and YouTube. The justification: “marginalized communities” need EFF on those platforms. Their statement gets this digital ethics classification:
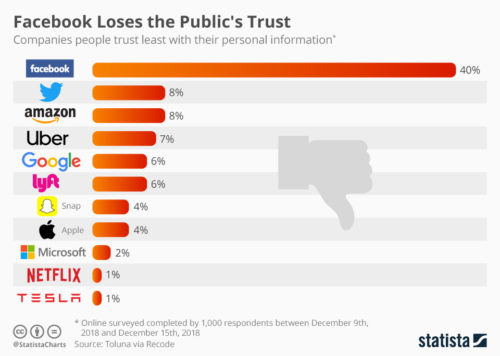
Their framing dissolves the moment you apply it consistently. If Musk firing the human rights team is disqualifying, Zuckerberg eliminating fact-checking and inviting Trump to dinner should be equally so. TikTok is called Chinese state-adjacent surveillance infrastructure. The EFF would be suing if… it were a US government program. The difference between X and Facebook is NOT principle. The difference, by their own admission, is that Facebook still delivers traffic.
The personnel history clarifies the relationship. In January 2019, Nate Cardozo, EFF’s senior information security counsel and a prominent Facebook critic, left EFF to become privacy policy manager at WhatsApp. The man who once wrote that Facebook’s business model “depends on our collective confusion and apathy about privacy” went to work for Facebook, precisely as the company was merging WhatsApp, Instagram, and Messenger into a single surveillance infrastructure. When I personally asked Nate what the hell, I got a shrug. Matt Stoller flagged it at the time: “You can say many things about EFF, but it’s not a tough critic of Facebook. EFF is a sometimes critic of and sometimes ally of tech giants.”
The criticism was crafted into a credential. The credential was the product. Facebook bought the critic to neutralize the criticism and acquire the legitimacy in one transaction.
Like a medieval indulgence: sin first, pay the church later, receive absolution.
The timing of the tight Facebook relationship with EFF deserves attention. On October 2, 2018, Saudi agents murdered Washington Post journalist Jamal Khashoggi at the Saudi consulate in Istanbul. The WhatsApp communications of Khashoggi’s associate Omar Abdulaziz had vulnerabilities exploited by NSO Group, surveilling their private conversations about Saudi activism.
The encryption campaign misstatements of Facebook were part of the surveillance chain that got a journalist dismembered. Four months later, Cardozo started his new job managing privacy law at WhatsApp. The company whose product had been exploited in a state-sponsored assassination hired EFF’s senior encryption counsel to clean up the mess created by Alex Stamos (after he quietly skipped town on the mess he left behind at Yahoo).
While EFF built up a credential as the place vulnerabilities were exposed and bad software went to die, suddenly Facebook was running the reverse play with the EFF lawyer in house. WhatsApp sued NSO in 2019. EFF filed an amicus brief in support of WhatsApp’s case, arguing NSO should not receive foreign sovereign immunity. In May 2025, NSO was ordered to pay $167 million in damages.
So EFF’s legal advocacy directly supported bad software by a giant corporation, asserting Facebook’s litigation position against NSO, while EFF’s former senior counsel sat inside WhatsApp managing privacy through the entire arc. The organization and the corporation were not adversaries. They were co-plaintiffs with a shared personnel file protecting Facebook, not the users and definitely not the hackers who exposed the deadly flaws in Stamos’ overheated encryption story.

Stamos was CISO at Yahoo during their existential breaches, they were disclosed after he abruptly left for Facebook. He was CISO at Facebook during Cambridge Analytica, atrocity crimes in Myanmar, as well as the deadly WhatsApp headlines discovered after he’d already left for Stanford. Stamos had never been a large operations-focused CISO before these two attempts, and left behind the biggest security failures in history. He not only failed upward, he used clean-up connections like Cardozo to plaster over the dumpster fires he left behind. Facebook staff asked to be reassigned away from Stamos such that he had nobody left under his remit by the time he was forced out of his second large operations CISO role attempt.
Declaration of Cyberspace Independence
EFF was founded in 1990 by John Perry Barlow, a Wyoming cattle rancher who both coordinated Dick Cheney’s congressional campaign, and wrote lyrics for the Grateful Dead. He authored “A Declaration of the Independence of Cyberspace,” a libertarian manifesto held up for decades as the organization’s ideology.
Cheney and the Dead were not the contradiction you might think at first glance. They’re the same move in different rooms. He accumulated access to the Republican power structure in Wyoming. He accumulated access to the counterculture power structure in San Francisco. Different aesthetics, identical function: get a seat at the table in any room where decisions get made.
Co-founder Mitch Kapor later acknowledged the founding tension directly: he believed in a role for appropriate regulation, but “John, at that point, was a pretty resolute libertarian; the less government the better. I lost that battle entirely… and EFF became, and was, staunchly libertarian.” Kapor left after internal conflicts in 1994 and went a direction that lacked the vinegar and bluster of EFF, while it silently made major improvements to the democratic infrastructure of the Internet.
The third co-founder, John Gilmore, coined the phrase “The Net interprets censorship as damage and routes around it.” In 2021, EFF’s board voted to remove Gilmore from governance for undisclosed reasons. Cindy Cohn’s announcement offered zero explanation. EFF publishes neither board minutes nor bylaws. An organization that demands transparency from every institution it scrutinizes applied exactly none to itself. They pushed out the man who co-founded the organization, believed in standing your ground, and replaced him with a PR campaign that tells people to leave when they don’t like something.
Run From Your Ground
Gilmore’s aphorism contains the test that EFF now fails. The entire cypherpunk premise is that you build your own infrastructure. You run your own servers. You don’t give away your ground to centralized platforms controlled by corporations. Imagine libertarian ranchers selling all their land to remote barons and just paying a usage fee. EFF’s own tools have reflected the point they are supposedly making: Certbot for self-hosted encryption, Privacy Badger against tracking, Surveillance Self-Defense guides. The technical output says: own your infrastructure. The Cohn book tour says shut your mouth and obey or leave.
The communications strategy doesn’t fit the brand at all. A principled digital rights organization in 2026 would operate from eff.org, a Mastodon instance, email lists, and RSS feeds. Every centralized platform represents exactly the concentrated power the cypherpunk movement was designed to resist. Choosing which billionaire’s platform to grace with your presence is not digital rights advocacy. It is social networking of upwardly mobile professionals seeking brand management to cross a velvet rope, the literal inversion of a digital rights defense.
Room 641A
Once upon a long time ago a 5G backbone in San Francisco unavoidably had a legal “grey zone” between the raw Internet and the neighborhoods connected to it. A Tor exit node showed up in that space. When I mentioned it to the EFF at one of their regular parties they casually asked if there was a way to get access so they could surveil plaintext traffic for “research” on who wasn’t safe. It was just a laugh at the time, I suppose.
However, a Tor exit node is a trusted and privileged observation point. Whoever sits on it sees every connection passing through. Asking to occupy a core network position “for research” sounds to me like surveillance access with a rather odd, untrustworthy, justification. Where else were they “joking” about this and based on what ethics or transparency for such a “research” model?
This is the same structure as the 2006 NSA’s Room 641A at AT&T, which EFF litigated against for years. Different scale, yet the same architecture. The nonprofit language, instead of a national security letter, didn’t wash with me at all. This was not what I expected from the EFF, not at all, but I probably should not have been surprised.
Known Wolves
In 2014, EFF helped overturn the conviction of Andrew “weev” Auernheimer on appeal, framing the case as essential CFAA reform and coder’s rights. Six months after EFF helped free him, weev published an article on The Daily Stormer identifying himself as a white supremacist and neo-Nazi. He became the site’s webmaster. He sent swastika-adorned flyers to thousands of printers at universities across the country. He called for the slaughter of Jewish children on a Nazi podcast.
EFF never revisited the case. A curious one, indeed.
Morgan Marquis-Boire, known online as “Morgan Mayhem,” claimed to have co-founded Kiwicon, New Zealand’s hacker conference. On the afternoon that I accepted an award from them for best-dressed speaker, the people in the New Zealand security community surprised me when they said… he didn’t. I took the award as kindly mocking me, from an environment that keeps things real. Morgan apparently had left to rapidly advance, by taking solo credit for other people’s work, and parlayed the association into advisory titles at EFF, the Freedom of the Press Foundation, First Look Media, and Citizen Lab. It all came crashing down November 2017, when The Verge corroborated ten separate allegations of sexual assault against him. EFF released a single statement of disassociation.
People at Kiwicon were far too modest and polite to specify details, yet they were unsurprised. His predatory behavior in the Kiwi hacker and goth scenes stretched back to at least 2009, years before those titles. The question is not whether EFF knew of his risks. The question is what kind of organization fails at transparency, fails to know what everyone at Kiwicon said they already did.
There Is No Outside
Alex Stamos seemed to have used his EFF association to rapidly stand up a protest conference across the street from RSA San Francisco, which then pivoted into Yahoo’s CISO role. It was a disastrous move. The conference never happened again, and Yahoo became riddled with undisclosed breaches that compromised over a billion accounts. When he infamously quit silently to take the CISO role at Facebook, his legacy became Cambridge Analytica, Russian election interference and WhatsApp encryption end-run.
There is no outside to this path. EFF, Yahoo, Facebook, Google, Freedom of the Press Foundation formed a network of organizations of different letterheads with boundaries blurred. The head of security at Twitter, leaving behind a dumpster fire there, picked up the Yahoo CISO job from Stamos, before rotating into leading security for the Democratic Party in the run-up to the second Trump win. People circulated through advocacy, corporate, and academic positions, accumulating credibility to spend at the next. A “digital rights” label became lubricant that makes a certain rotation frictionless for some, without evidence of outcomes aligned with meaningful defense of rights.
Letters of Marque
A privateer is a pirate with a government license. Not the democratic, distributed ships of actual pirates, but ruthless mercenaries in privileged positions, milking corrupt systems for personal gain while claiming the crown made them unaccountable.
The pattern across three decades of the EFF is an organization that exists at the intersection of opposed power networks that they operationally feed to each other. They raise whatever flag on their mast convenient without real accountability. Silicon Valley needs a civil liberties organization to legitimize its resistance to regulation. Washington needs a tech-literate interlocutor that bridges regulation to those opposed to it. EFF becomes a ship of privateers that floats adjacent to victims, never landing to own the risks. Not a watchdog. A mercenary team unmoored.
I say this because I wonder if we can ever know if EFF has been corrupted or has EFF been captured? The real answer is that a distinction doesn’t matter to the people harmed. Whether a ship flies a false flag by design or by drift, the powerful cannons still fire into the lives of the same vulnerable people.
Leaving X costs them nothing. There is no evidence Musk is funding EFF. Meanwhile Google and Facebook came under fire as big “donors” to EFF, let alone their lawyers being offered jobs. And then Meta’s ecosystem generates the engagement that justifies EFF’s social media budget. The departure from their Twitter account is a loyalty signal to the donor network that writes checks, wrapped in the language of the network that generates moral authority.
The libertarian framework supposedly protected Internet users from government over-regulation for two decades. The progressive frame now protects these relationships from an opposite direction. The ideology rotates, as the function persists. The function is gaining access to power, serving power, while claiming to protect the people that power displaces.
Tim Sweeney, founder of Epic Games, mourned what EFF “once was.” Shutterstock founder Jon Oringer demanded his donations back, exposing his own selfish mindset. His concept of “donations” meant expecting specific returns with his money. They’re both wrong about the direction of EFF’s drift but also right about the betrayal. EFF’s principles were instrumental, deployed selectively to serve those funding their operation at any given moment.
Read the EFF blog post logic carefully and you can see it fall apart right before your eyes.
On Facebook, Instagram, and TikTok, EFF says: we stay despite disagreeing with these platforms, despite their surveillance business models, despite their suppression of marginalized voices, because the people there need us. Staying is framed as fighting. On X, EFF says: engagement collapsed, the platform is diminished, we’re leaving. Leaving is framed as principle.
Apply the logic consistently, and it can’t hold true.
If “stay and fight for the marginalized” is the principle, stay on X. The marginalized are there too. If “leave toxic platforms” is the principle, leave Facebook. Its harms are documented and ongoing. The only principle that explains both decisions simultaneously is return on investment. They stay where the numbers work. They leave where the numbers don’t. That’s it.
What is this if it isn’t libertarian? This is where it gets interesting for historians. EFF is signaling a political view that maps to whoever pays most to punch down. Serve when it pays back directly at no risk. The moment service costs something real, the moment the engagement metrics crater, the moment the platform stops generating traffic for your fundraising operation, you leave and call that ethics. The marginalized are used as a justification, not a constituency. You give only when the getting is better, which is a value extraction model.
EFF freed a Nazi. The ACLU never made the Skokie Nazis advisors, never hired them, never failed to publicly reckon with the consequences. EFF didn’t just defend weev’s legal rights. They ran a #freeweev campaign that personalized the Nazi cause around the Nazi individual. That’s advocacy for a Nazi, not a principle. And they never revisited it. Their silence on the whole matter has been the problem, not a defense of principle.
EFF harbored a predator.
EFF sold their senior counsel to the company whose platform helped get a journalist murdered.
EFF purged their co-founder without explanation.
EFF demands transparency from every institution except themselves.
And when the EFF outgoing director went on national television and was asked how to fight for rights and protect people from algorithmic harm, her answer was: run away.
That is not a digital rights organization. You probably know the words that describe it better. The refusal to testify, the refusal to account, the refusal to reckon. The Gilmore removal with no explanation. The Marquis-Boire disassociation with no accounting. The weev case never revisited. The Tor surveillance request with no transparency framework. The silence is the story for a “transparency” organization operating as if it doesn’t apply to them.
What does a real digital rights organization look like? It stands up its infrastructure because it runs as its own space. It fights where victims stand, not where engagement metrics pay. It applies every transparency demand it makes of others to itself first. It publishes its board minutes, its bylaws, its donor list, its conflicts of interest. It doesn’t tell a victim to leave if they don’t want to be harmed. It never sells its lawyers to the companies it scrutinizes. It never personalizes a legal campaign around a defendant it hasn’t vetted. It reckons publicly when its work produces harm. It builds tools that distribute power instead of collecting credentials that concentrate it. And it measures its success not by impressions, not by traffic, not by book sales and talk shows, but by whether the people it claims to protect are safer than they were before.
A real digital rights organization tells the truth, especially about why it retreats.