Joshua Maddux tweeted easily reproducible evidence that the Facebook app turns on your iPhone camera without notifying you and at times you weren’t expecting. TNW picked up the story:
By now, everyone should be well aware that any iOS app that has been granted access to your camera can secretly record you. Back in 2017, researcher Felix Krause spoke to TNW about the same issue.
At the time, the researcher noted one way to deal with this privacy concern is to revoke camera access (though that arguably doesn’t make for a smooth software experience). Another thing he suggested is covering up your camera — like former FBI director James Comey and Facebook‘s own emperor Mark Zuckerberg do.
Before saying that everyone should expect allowing “emperor Zuckerberg” access to your camera means he will spy on you, however, the author backs down and says it’s unclear whether Facebook secretly taking video is to be expected by iPhone users.
It remains unclear if this is expected behavior or simply a bug in the software for iOS (we all know what Facebook will say; spoiler: “Muh, duh, guh, it’s a bug. We sorry.”). For what it’s worth, we’ve been unable to reproduce the issue on Android (version 10, used on Google Pixel 4).
See my earlier post on neo-absolutist card indexes for a historic reference of what life was like for those who couldn’t quit Facebook of the 1800s.
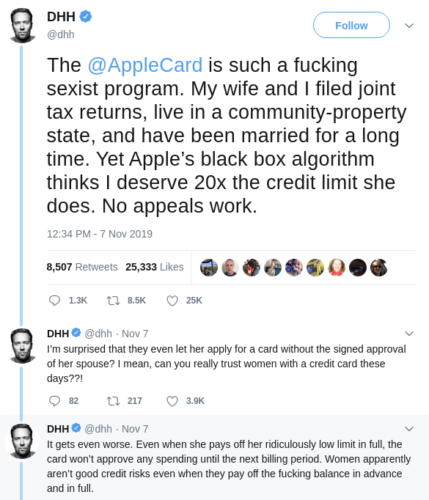
One reason Facebook could repeatedly issue blanket denials “we don’t use your sensors for ads” could be that they shovel meta data into analytic engines, and sell that to affiliates. Those other companies pay for the meta data. Someone else advertises to you, through this tortured logic.
Would that enable Facebook to claim they don’t consider themselves to be using the data for advertising? We’d have to do a deeper line of auditing to find out for sure. Looking at transfer of data is not enough anymore, as analytics increasingly can be done onboard mobile devices including drones collecting massive amounts of sensor data.
This also means Facebook could claim they have no evidence of photos, videos, etc being transmitted to them, while transmitting rich meta data about users based on sensor capture.
See this example thread, which claims Spotify was the one who decided to target ads.
The most direct question is whether Facebook is able to use listening to sell data to companies like Spotify as profile/targeting meta information, without revealing to Spotify or anyone else that a microphone or camera actually was used?
Updated: An official explanation has been posted:
We recently discovered that version 244 of the Facebook iOS app would incorrectly launch in landscape mode. In fixing that issue last week in v246 (launched on November 8th) we inadvertently introduced a bug that caused the app to partially navigate to the camera screen adjacent to News Feed when users tapped on photos. We have seen no evidence of photos or videos being uploaded due to this bug. We’re submitting the fix for this to Apple today.
And again Facebook doesn’t say there was no evidence of photos or video generating data, storing data or sending data, especially meta data or notes about what the camera could see. It says more narrowly that the photos and videos themselves weren’t uploaded.