I’ve been asked to comment on OpenClaw a few times. And to be frank I’m not that interested. It’s felt like making a comment on Coleco Cabbage Patch Kids in 1983. I know it’s all the rage, just like those dolls, but really?
Alas, as much as I can wish OpenClaw was just a fad it has over 300,000 GitHub stars, a Nvidia keynote, and an OpenAI acqui-hire. The architectural flaws baked in suggest we will have to deal with it for a while. At GTC 2026, Jensen Huang practically called OpenClaw the future of everything:
…the largest, most successful, and most popular open-source project in history.
Please. Not even close.
He tried to juice the audience:
Every company in the world today needs to have an OpenClaw strategy.
Yeah, right next to their Cabbage Patch Kid display cabinet.
Sam Altman acqui-hired its creator. Nvidia built a free security wrapper around it. CNBC rubber-stamped the hype by declaring the Lobster-themed dumpster fire “the next ChatGPT.”
Ok, so I guess it’s not going away. People are going to keep asking me about this. Here’s what I think: OpenClaw is three months old and has 29 GitHub Security Advisories. That’s roughly one every three days since launch. Do we all understand how horribly bad this is?
It has had a one-click remote code execution vulnerability that exposed over 220,000 instances, a skills marketplace where up to 900 packages were malicious, and no third-party security audit.
Oh, but all that’s just bugs, you say. Watch as they are fixed, you say, just like how fire, ready, aim companies always work out fine for safety in the end.
Let’s be honest. We’re talking about a tool that unsafely grabs access to your WhatsApp, Signal, iMessage, Telegram, Slack, and email. It immediately lowers all your safety, undermines decades of work to provide privacy.
OpenClaw Is a Threat
OpenClaw likes to describe itself as a “personal” AI agent because it runs on hardware you provide. You give it a laptop and a VPS, and it connects to your messaging platforms. Then it slurps up all your messages, responds on your behalf, takes actions, runs tools. It’s a “personal” agent taking control over your entire digital communication life.
The value proposition is billed as autonomy. Instead of paying OpenAI or Anthropic for cloud-hosted agents, you run your own locally, deflating the market with cheaper open-weight models, by managing fleets of always-on agents across every messaging channel you use.
And the glaring problem is how “personal” and “local” are being used when your agent is actually holding plaintext read/write access to every private communication channel you own.
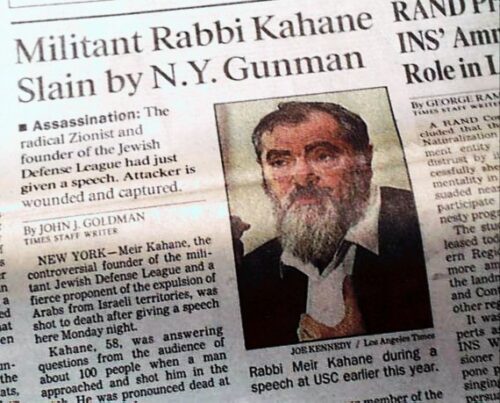
Why am I reminded of the Austrian Emperor mindset? Remember the guy who had spies chasing everyone in Vienna, filling out little note cards on their lives, all for him to stay in power?
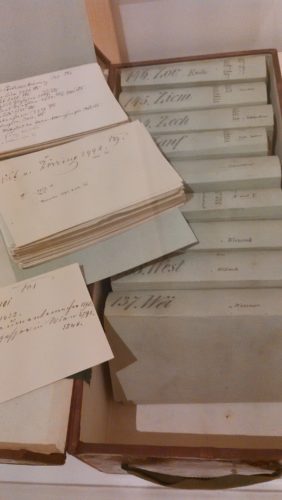
A centralized espionage card index for surveillance of residents is literally what OpenClaw built. I’m told the developer was someone “under-the-radar” from Austria.
Where Encryption Dies
Signal spent years making end-to-end encryption so easy nobody had a reason to avoid it. WhatsApp licensed the Signal protocol to protect even more messages in transit (despite putting a backdoor in it for Facebook). iMessage runs its own E2EE implementation. These platforms made enormous investments to ensure privacy in messaging.
OpenClaw watches at the endpoint for decrypted content, appropriating the authorized view of the user themselves. That’s how it works, without apology. An agent can’t respond to a message without reading it first, but this goes all the way to reading everything in plaintext. All of it.
That means the correct description of OpenClaw is a plaintext aggregator to undermine all encrypted channels. Intelligence agencies know what I’m talking about and they most certainly are salivating at the new greenfield of exposed targets. The “claw” consolidates every protected conversation you have, whether personal, professional, privileged, or intimate into a single static authentication token on a personal device.
The token is generated with the usual cryptographic entropy. It uses timing-safe comparison. But it never rotates. There is no expiry. There is no per-channel access scoping. There is no session management.
One token to rule means all channels, forever, until you would decide to manually change it. And if you don’t know you’re totally compromised, that ain’t gonna happen. And the gateway’s authentication rate limiter exempts localhost connections by default. A process on your machine can brute-force the token with no throttle and no lockout.
The encryption properties the security industry spent decades rolling out all get an OpenClaw ripping their safe door off its hinges and replacing it with… nothing.
Deck Chairs on the Titanic for Sale, Cheap
In late January 2026, less than two months after OpenClaw’s public launch, a security researcher named Mav Levin of DepthFirst disclosed CVE-2026-25253. It was a one-click remote code execution vulnerability with a CVSS 8.8 score.
Here’s how it worked. You visit a malicious webpage. The page’s JavaScript connects to your local OpenClaw instance via WebSocket. The server doesn’t validate the origin header, so it accepts the connection. Your authentication token is exfiltrated in milliseconds.
Oops.
The attacker has your all-powerful token. So they connect to your gateway, disable your sandbox, disable user confirmation prompts, escape the Docker container, and execute arbitrary commands on your machine.
OpenClaw for full system compromise.
The vulnerability existed because OpenClaw’s Control UI accepted a gateway URL from a query string parameter and automatically connected to it, sending the stored token, without any validation.
Users running OpenClaw on localhost were thinking they were safe because the server wasn’t exposed to the internet, yet they were vulnerable. Using a single browser for everything is how attacks would bridge from public to private access.
Penligent counted over 220,000 exposed instances. SecurityScorecard’s STRIKE team confirmed 15,200 vulnerable to RCE.
And what does OpenClaw do to help detect this kind of game over situation?
Nothing.
There is no audit trail. The only logging mechanism records user-issued slash commands. There is no record of what the agent reads, sends, or does. A compromised instance leaves no forensic record of what was exfiltrated.
I told you attackers were getting excited.
Flawed Market Exposure
OpenClaw’s extensibility runs through ClawHub, a skills marketplace. Anyone can publish a skill. The only requirement is a GitHub account older than one week. You know, because one-week-old is such an important line to draw in safety terms.
Koi Security audited all 2,857 skills and found 341 that were outright malicious. Of those, 335 traced to a coordinated campaign called ClawHavoc that delivered Atomic Stealer, a macOS credential-stealing malware, disguised as legitimate tools. Bitdefender’s independent scan put the number closer to 900 malicious skills. That’s roughly 20% of all packages in the ecosystem.
I suppose macOS showed up because there have been so many articles recommending people run OpenClaw on cheap Apple hardware.
A separate analysis by ClawSecure found that 41% of the most popular skills contain security vulnerabilities, with 30.6% rated HIGH or CRITICAL.
Yikes. Let’s do the math on that threat model.
So the third-party extension ecosystem for a system with access to all your private messages had a one-in-five chance of being actual malware, and a two-in-five chance of having serious security flaws. Within weeks of launch.

OpenClaw’s skill security scanner consists of eight regex rules. There is no cryptographic signing, no sandboxed execution analysis, no dependency scanning. The entire defense between a malicious skill and your private messages is a… grep.
The project’s own codebase contains no reference to ClawHavoc even though it was the coordinated campaign that weaponized 335 skills in its marketplace.
The largest attack on its ecosystem has been completely unacknowledged in its own repository.
Lethal Trifecta Time
Palo Alto Networks mapped OpenClaw against the OWASP Top 10 for Agentic Applications and identified what Simon Willison called a “lethal trifecta”: private data access, untrusted content exposure, and external communication capabilities, all in a single process.
The ClawHavoc campaign demonstrated the pattern of hundreds of malicious skills, masquerading as legitimate tools, delivered credential-stealing malware through the same pipeline that handles your private messages. The “double agent” behavior looks like a normal “private” and “local” agent because it is normal.
That’s the whole rub of this completely broken business logic. The credentials are real, the API calls are sanctioned. EDR records a normal process. No signature fires. Nothing went wrong by any definition your security stack understands. Prompt injection runs like a backdoor, in other words, when an attacker embeds instructions in an email or message, the agent reads it as part of normal operation, and follows the injected instruction using its own tokens through sanctioned channels.
Before being named to the role, Jamieson O’Reilly of Dvuln was one of OpenClaw’s most effective adversaries. He used Shodan to find 900+ exposed instances leaking API keys with no authentication. Then he built a proof-of-concept malicious skill called “What Would Elon Do,” artificially inflated its download count to #1 on ClawHub, and watched developers from seven countries install it and execute arbitrary commands. Steinberger’s response was to hire him. O’Reilly is now listed in OpenClaw’s own SECURITY.md as the project’s Security and Trust lead. And here’s what he said about the design he was hired to fix:
closing context leakage requires deep architectural changes to how untrusted multi-agent memory and prompting are handled.
The project’s own security lead is admitting the architecture is fundamentally insufficient for basic safety.
Governance? What Governance?
Token Security found that 22% of its enterprise customers already have employees running OpenClaw without IT approval.
Uh oh.
Bitsight counted more than 30,000 publicly exposed instances in two weeks. Censys found the largest concentrations in the United States, China (30% on Alibaba Cloud infrastructure), and Singapore.
We’re screwed.
OpenClaw’s own documentation states:
There is no “perfectly secure” setup.
Haha, nice try. Don’t let perfection be the enemy of good, is the right thing to say here. Who thinks anything is ever perfectly secure?
The security model is perfectly dumb. It assumes the host is a trusted boundary and the operator is trusted. It was designed for a lonely hobbyist running an agent on their laptop with nothing to lose. That somehow got pivoted into enterprise employees with access to corporate communications, by developers with access to production credentials, and lately… journalists with sources, lawyers with privileged communications, activists in hostile states, and abuse survivors whose location is in their messages.
These people chose encrypted messaging platforms because privacy is a right and content is sensitive. OpenClaw throws all the lessons out the window to offer a tragedy, a single point of failure.
Death From 1,000 Hot Takes
CNBC ran a piece with lots of people who are all celebrating this. It featured Gavriel Cohen, an Israeli developer who loved OpenClaw so much he decided he would make a secure fork (NanoClaw) because he cares about his business data. What CNBC glossed over is that Cohen discovered that OpenClaw had downloaded all of his WhatsApp messages, including personal ones, and stored them in plaintext on his computer. Why? That’s the design decision.
Cohen was so impressed by this failure he shut down his AI marketing firm to sell a fix. The article framed this as an entrepreneurial success story. Read it again: the most technically sophisticated user in the excited promotional coverage noticed all his private messages in cleartext on disk and he refused to use the shipping product.
Nvidia’s response was NemoClaw, offering free security services wrapped around OpenClaw, to get enterprise customers to drop their guard. DigitalOcean launched a one-click deploy with “security baked in from the start,” because the project notoriously doesn’t have it. Six independent security teams rushed to ship six OpenClaw defense tools in 14 days.
Everyone is in a rush to sell a fancy lock. Nobody is talking about the door being made of toilet paper.
The acqui-hire of Peter Steinberger, OpenClaw’s creator, so that the project will transition to a foundation that OpenAI would “continue to support” is bad news. This neutralizes a competitive threat while claiming credit for stewardship.
The project still has no third-party audit. Its disclosure process still has no SLA. A third of its open security issues are stale. The static token still doesn’t rotate. OpenAI consolidating the project makes the architectural flaws harder to fix because now there’s a bigger organization with more inertia invested in a completely broken design.
The Emperor of Austria at least had the decency to keep his espionage card index in a monitored locked cabinet. OpenClaw leaks the key without a record and doesn’t even rotate it.
Take it From Experience
New projects always ship with security gaps. That is a normal and understood state of engineering. My frustration has nothing to do with OpenClaw bugs, as every project ever has had and will have bugs.
The critique is that someone designed an access level completely incompatible with “security comes later.”
A new game can ship without a security audit. A new social network can ship with a static token. A system that consolidates plaintext read/write access to all of a user’s encrypted messaging platforms behind a single credential on a personal device, with autonomous write capability, MUST NOT.
The relationship between access and safety governance is the entire question. OpenClaw started from 1800s Austrian Emperor like access and is thinking about what governance could look like after the fall of monarchy. Nvidia keynotes and OpenAI partnerships and CNBC profiles are rushing in the opposite direction, past the point where the security maturity can protect the people using it.
Adversa.ai put it plainly:
OpenClaw is “one of the most dangerous pieces of software a non-expert user can install on their computer.”
Jensen Huang called it Linux. Linux doesn’t have access to your Signal messages.