Lately I have heard people complaining about their friends and family who can not or will not patch the Jeep software.
I suspect the more people that look at the process for patching Jeeps the more the process will improve and increase the likelihood of patching. So here are a few quick steps that might be helpful.
First
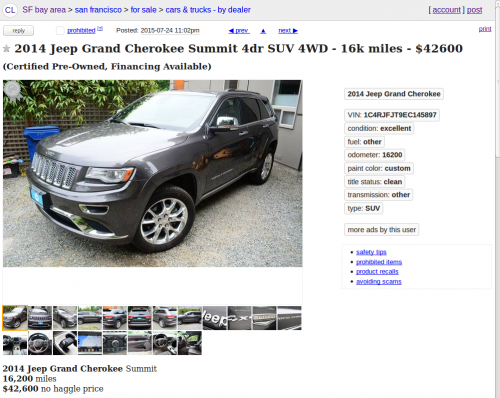
You need a Vehicle Identification Number (VIN). You can ask your friends or family for their VIN. You can walk into a parking lot, especially a Jeep dealer’s, and look at the VIN. Or you can search craigslist for a VIN. I used the SF bay area site but you can search anywhere using a simple URL modification:
https://sfbay.craigslist.org/search/cta?sort=rel&min_auto_year=2014&query=jeep
Mine brought up a good candidate to check almost immediately, and you can see the VIN (1C4RJFJT9EC145897) right at the top:
Second
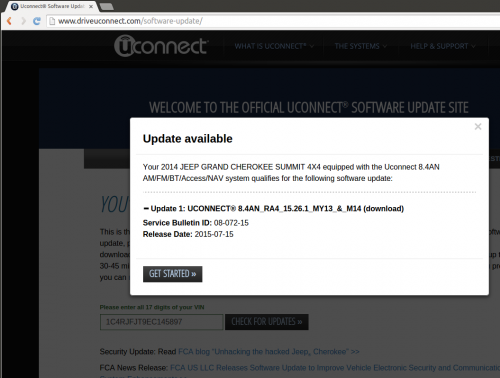
Copy the VIN number and enter it into the Uconnect Software Update page. If the vehicle with the VIN you found needs an update, you will see the success window:
Speaking of vulnerabilities and missing patches, you probably will have to use IE. Chrome errors out and UConnect is up front about the fact it does not support Firefox after version 37 (current Firefox is 39).
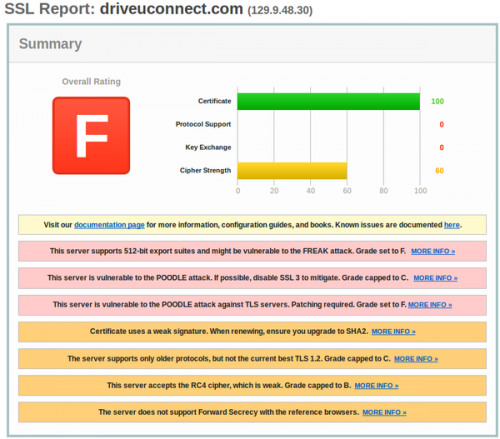
You also should note that attempting to use HTTPS reveals UConnect has an horribly insecure setup — a mis-configured service far behind on critical fixes.
I believe I was the first person to point the UConnect flaws out but again this whole process really should be something many people are assessing on a frequent basis. POODLE vulnerability shouldn’t have to be “discovered” by me months after it was announced.
Anyone else find a big red F for car manufacturer site safety less than confidence inspiring? I really should insert a graphic here of a crash-test-dummy flying out the window…
Third
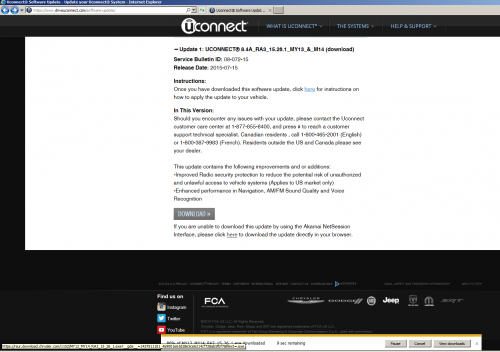
Now comes the tricky part because of the browser support issues I mentioned earlier. UConnect tries to force you into using a convoluted and slow graphical process to reach the update file.
UConnect seems to want to make some sort of case to install Akamai software before you can download the patch. Someone must have thought that is a good way to deal with a rush by 1 million owners suddenly trying to grab a 380MB file. In reality that is nothing compared to the number of people downloading larger files (e.g. movies) all the time through caching services invisible and compatible with any browser.
The Akamai client really doesn’t make any sense and just slows down the process so I avoided it by downloading from Microsoft a virtual machine running IE (e.g. Windows7 with IE 10 is a 3.5GB VM) and clicking through the UConnect “Tutorial” pages quickly until I was able to get to the end. That is where a direct download link finally appeared.
When I tried first with Chrome I was greeted with this warning:
IMPORTANT: The Akamai NetSession Interface is not compatible with your current browser. You can download software updates by clicking the direct download link for each available update.
And then, instead of any direct download link at the end of a bunch of clicks, Chrome fails with this warning:
An unexpected error has occurred. Please try refreshing your browser and entering your VIN again. If the issue persists, please contact UConnect customer care center at 1-877-855-8400, and press # to reach a customer support technical specialist. Canadian residents , call 1-800-465-2001 (English) or 1-800-387-9983 (French).
It probably would save a lot of time if UConnect just said at the start IE is the only supported browser; because really the UConnect site is designed only to work with old insecure versions of IE.
I was basically wasting time trying to get safer and newer browsers to work with the interface. Chrome stalls out at the end and Firefox doesn’t even get off the ground. If you try curl/wget…LOL
Anyway, back to trying to actually get a patch, IE reveals a fancy button graphic as well as an actual link to an actual file.
Fourth
After all that wasted time trying to get through the UConnect web interface quagmire, I finally clicked on a link. Notice at the bottom left of the page a tiny URL reveals a token has been generated:
http://rsur.download.chrysler.com/1152/MY13_MY14_RA3_15_26_1.exe?__gda__=
1437511101_4a9001e63d28e5ce6214cf728ab5fbf7&filext=.exe
This URL can be copied from IE into Firefox or Chrome and the download works fine. And the token seems to expire so you can’t use the same one I generated. I would have to post the file for you to download from a file sharing site instead of just giving you the authoritative source.
It all really begs the question of why there is so much fluff, obfuscation, client software and tutorials instead of a simple download link via an invisible caching service compatible with everything.
Fifth
Once the 390MB “MY13_MY14_RA3_15_26_1.exe” file is downloaded you may notice it is just a 7zip self-extracting archive. So use 7zip to unpack the archive and you have a 580MB “swdl.iso” file. Simply use 7zip again to extract the iso. This results in a manifest file from June 23, 2015 and four folders:
- bin
- etc
- lib
- usr
At this point you’re in the position to post the ISO to a file sharing site and invite people on a Jeep owners forum to install it from your source. Apparently that is already happening, which is easy to understand given how painful it is for owners to go through the above process.
Or you can read the files and learn more about how to help your friends and family stay safe.
For example, use a text editor to open the manifest file and scroll to the bottom. Here you should see options that indicate you can set the patch to autoupdate (no human intervention):
reset = “bolo”, — what type of reset is required
autoupdate = false, — automatically invoke the update (no HMI needed)
As another example, navigate to the usr/share/SKINS/ directory and you can find the “swf” (flash) themes available:
Abarth, AlfaRomeo, Chrysler, Dodge, Ferrari, Fiat, Jeep, Lancia, Maserati, Ram, SRT, Viper
Or move deeper into usr/share/SKINS/fontSwfs and read the file called “EVALUATION USE LICENSE AGREEMENT.doc”
1. You may install and use the bitmap fonts contained within the Evaluation Font (“Fonts”) internally for the sole purpose of evaluating the functionality of MONOTYPE products.
2. You may not rent, lease, distribute or sublicense the Fonts without first obtaining a written license from Monotype Corporation.
We have to assume a written license was obtained, while leaving the evaluation license anyway. Maybe Monotype requires the eval license to ship with the fonts? Still I feel like I have opened the hood of a car and found foam packing material that was meant to be removed.
Have a look into /usr/share where you will find “install.sh” with some interesting commands and comments
# File must be less than 2K bytes for security reasons!
What happens if the file grows larger?
I found a few network scripts yet none that offered firewall or service port options. “STATIC_IP=192.168.57.99” shows up in a template while “STATIC_IP=192.168.6.1” is in a shell script.
And I found a spelling error. This is Line 13 of network.sh:
echo “mouting desktop…..”
A peek into /usr/share/scripts/update/installer will bring you to a compiled “system_module_check.lua” file that the car trusts to help prevent the wrong update being used.
It’s trivial to decompile lua and look closer. Grab the latest unluac.jar file and run it against the file you want to read. For example:
java -jar unluac_2015_06_13.jar system_module_check.lua > decompiled.lua
With this you can read the error levels and checks in the new decompiled.lua file
L8_9 = “Model Year Not set in ISO”
Also have a look into /usr/share/MMC_IFS_EXTENSION/bin because this is where you find more scripts and binaries of interest. Here is the check_temperature.lua:
require "service" resp,err = service.invoke("com.harman.service.OmapTempService", "getOmapTemperature", {} ) if (err == nil) and (resp.omapTemp ~= nil) then -- print("Temperature is ", resp.omapTemp) if(resp.omapTemp > -20) then
os.exit(0) — temperature is acceptable
else
os.exit(-1) — temperature is NOT acceptable
end
end
Temperature “NOT acceptable” level seems like something that should not be easily modified. The obvious question I have with these files:
Is Chrysler ok with people editing/improving the files and delivering their own patch to the Jeep community (as already may be happening), to encourage after-market service and support options? Could we reasonably expect independent auto mechanics to also fix code?
Conclusion
I found this five-step process of getting a patch unnecessarily complicated. A download link should not be so obscure to find and incompatible with the latest/safest browsers. Also I found the patch strangely lacking integrity protections. And so you may want to consider the details of this patching process and have a closer look in order to help friends and family update their software and stay safe.
Updated to Note: Good news! Earlier one of my big questions, as I had wondered aloud, was whether an algorithmic method was used to verify the ISO file. I found the answer is yes, by looking in /usr/share/scripts/update/isochk.lua
openssl rsautl -verify -inkey /etc/keys/swdl.pub -in /tmp/a -pubin -out /tmp/b
hashFile sha256 /fs/usb0/swdl.iso /tmp/c

Sounds like you recommend waiting for the USB in the mail?
Good question! Sorry I left that out.
Yes and no. I recommend more people go through the download process to give feedback and improve it.
Someone sending you a USB that arrives before an “official” one is a possibility and how would you know not to trust what you get in the mail? The integrity check of the ISO on that USB could protect you against a malcious one.
However, how will the USB-in-the-mail process verify authenticity of the sender? It probably relies on identification details about the recipient (VIN, address, date of purchase) but any formal-looking letterhead in a fancy box with fancy USB would look legitimate.
Using the online download process has a better chance, and far more cost-effective methods, of establishing authenticity of the file sender/server you need to trust. It adds another authentication layer that regular physical mail lacks.
With that said the online process is broken and is risky. However, I still recommend consumer pressure be applied ASAP to improve the online system, which means using it and providing feedback.