At least four platforms now compete for the right to run autonomous agents against your messaging channels and business data. One of them has 341,000 GitHub stars. Does that mean anything?
The Star
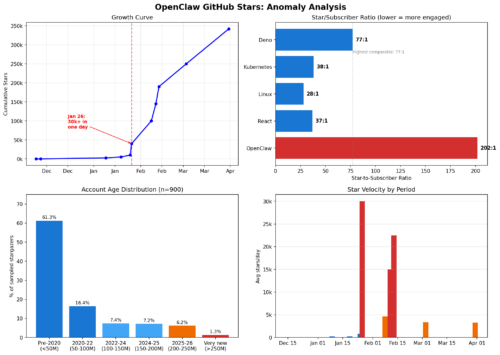
OpenClaw is the most-starred software project on GitHub. Most. Biggest. And NOT in a good way. Like the Titanic way. It passed React’s 13-year record in 60 days. On January 26, 2026, the repository gained at least 30,000 stars in a single day. Suspicious? Every star from #10,000 through #40,000 in the GitHub API carries the same date. Independent analysis of the GitHub Archive found multiple single-day jumps above 25,000 stars, a pattern that typically signals, wait for it, scripted starring.
The sharper number is the one GitHub doesn’t put on the front page. OpenClaw has 341,000 stars and 1,691 subscribers. A subscriber is someone who chose to watch the repository. They get notifications, they follow development. The star-to-subscriber ratio is 202:1. For comparison: Linux is 28:1. React is 37:1. Kubernetes is 38:1. Deno, the highest comparable outlier, is 77:1. OpenClaw’s ratio is nearly three times the next worst.
341,000 identities clicked a button. 1,691 are paying attention. That makes it the worst repo, and by far.
What the Star Belies
Anthropic’s Claude Code is a strong agent platform, yet it’s vertically integrated as one provider. The head-to-head that matters now is the one between the sudden and suspicious market darling and the secure alternative I just built to replace it.
| OpenClaw | Wirken | |
|---|---|---|
| Channel isolation | NONE. Single process, single token, all channels. | Compile-time. Separate OS process per channel. Cross-channel access is a compiler error. |
| Blast radius | NONE. Everything. Infinite. | One channel. |
| Credential security | NONE. 220,000+ exposed instances. | XChaCha20-Poly1305 vault, OS keychain, per-channel scoped, rotating. |
| Credential leak prevention | NONE. | Compiler-enforced. SecretString: no Display, Debug, Serialize, Clone. Zeroed on drop. |
| Audit trail | NONE. | Append-only, SHA-256 hash-chained, pre-execution. SIEM forwarding. |
| Tamper detection | NONE. | Hash chain breaks on any modification. |
| Skill signing | Optional. 824+ malicious skills (20% of registry). | Ed25519 required. |
| Sandbox | NONE. | Docker or Wasm. Ephemeral, no-network, fuel-limited. |
| Inference privacy | Provider DPA. | Operator control: DPA, TEE, or local. |
| Dependency | Node.js. | No runtime dependencies. |
| OpenClaw skill.md parsing | Native. | Native. |
A note on inference privacy: Tinfoil and Privatemode run open-source LLMs inside hardware TEEs (AMD SEV-SNP, Intel TDX, Nvidia H100/Blackwell CC). Hardware enclaves get broken by sophisticated side-channel. But the choice being offered is enclaves versus a provider who just promises not to look. A side-channel requires targeting and real effort. Reading prompts from a database requires nothing more than a query. TEEs are an option, they make exfiltration expensive instead of free. If you want zero cloud exposure, point Wirken at Ollama and keep everything local.
Stars measure clicks.
The table measures trust, in architecture.
Get Wirken: github.com/gebruder/wirken
Update March 20: Nvidia knows OpenClaw has a major problem. It released OpenShell to try and contain the flaws, but doesn’t fix the architecture inside it.
