Palo Alto Networks published its latest Defender’s Guide on May 13, claiming that scanning its own product code with Anthropic’s Mythos model under Project Glasswing produced a vulnerability disclosure cycle several times the volume of a typical month.
Today’s advisory covers 26 CVEs (representing 75 issues) versus our usual volume (typically less than 5 CVEs in a month); none of which are being exploited in the wild.
And then their own advisory feed at security.paloaltonetworks.com contradicts their guide in at least three ways. The CSV at security.paloaltonetworks.com/csv is authoritative for severity, CVSS scores, product, version constraints, problem descriptions, and publication dates. I rely on it as the primary source for everything that follows. Basically showing that Palo Alto disagrees with Palo Alto.
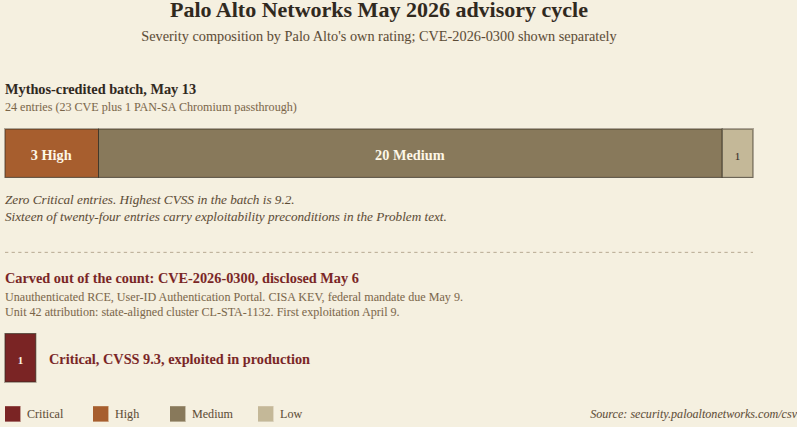
The CSV report for May 13 returns twenty-three CVE-numbered entries plus one informational bulletin numbered PAN-SA-2026-0007 covering the monthly Chromium passthrough update for Prisma Browser.
The blog said twenty-six. That’s a mystery gap of at least three. The CVE-2026-02XX sequence spans 0238 through 0265. The following give me an HTTP 404 with no redirect on the PSIRT portal:
- CVE-2026-0252
- CVE-2026-0253
- CVE-2026-0254
- CVE-2026-0255
- CVE-2026-0260
I can’t figure out yet whether these are being withheld pending coordinated disclosure with another vendor or assigned to a CVE Numbering Authority other than Palo Alto. I went looking for three and got stuck here.
All that being said, here’s the read-out. Severity is by Palo Alto. CVE-2026-0300 is included for context, but please note it does not get AI-credit and was disclosed eight days earlier. I’ll get to that in a second.
| CVE/SA | CVSS | Severity | Product | Class | Note |
|---|---|---|---|---|---|
| CVE-2026-0300 | 9.3 | CRITICAL | PAN-OS | Buffer overflow | active exploitation by CL-STA-1132; CISA KEV (added 2026-05-06); unauthenticated; disclosed 2026-05-05 |
| CVE-2026-0265 | 9.2 | HIGH | PAN-OS | Authentication bypass | CAS enabled on network-reachable mgmt iface; unauthenticated |
| CVE-2026-0264 | 9.2 | HIGH | PAN-OS | Buffer overflow (RCE) | unauthenticated; DNS proxy/server |
| CVE-2026-0263 | 9.2 | HIGH | PAN-OS | Remote code execution | unauthenticated; IKEv2 |
| CVE-2026-0262 | 8.7 | MEDIUM | PAN-OS | Denial of service | unauthenticated; Threat Prevention signatures block |
| CVE-2026-0261 | 8.6 | MEDIUM | PAN-OS | Command injection | admin-auth required |
| CVE-2026-0248 | 8.6 | MEDIUM | Prisma Access Agent | Certificate validation bypass | AitM positioning required |
| CVE-2026-0242 | 8.6 | MEDIUM | Trust Protection Foundation (ex-Venafi) | SQL injection | CyberArk-owned product line |
| PAN-SA-2026-0007 | 8.6 | MEDIUM | Prisma Browser | Chromium passthrough | upstream Chromium bundle |
| CVE-2026-0251 | 8.5 | MEDIUM | GlobalProtect App | Privilege escalation | local access required |
| CVE-2026-0247 | 8.5 | MEDIUM | Prisma Access Agent | Authorization bypass | |
| CVE-2026-0246 | 8.5 | MEDIUM | Prisma Access Agent | Privilege escalation | local access required |
| CVE-2026-0258 | 8.3 | MEDIUM | PAN-OS | SSRF | unauthenticated; IKEv2 cert URL fetching |
| CVE-2026-0257 | 7.8 | MEDIUM | PAN-OS | Authentication bypass | |
| CVE-2026-0250 | 7.7 | MEDIUM | GlobalProtect App | Buffer overflow | |
| CVE-2026-0244 | 7.7 | MEDIUM | Prisma SD-WAN | Certificate validation bypass | AitM positioning required |
| CVE-2026-0249 | 7.6 | MEDIUM | GlobalProtect App | Certificate validation bypass | AitM positioning required |
| CVE-2026-0240 | 7.4 | MEDIUM | Trust Protection Foundation (ex-Venafi) | Information disclosure | CyberArk-owned product line |
| CVE-2026-0241 | 7.2 | MEDIUM | Trust Protection Foundation (ex-Venafi) | Authorization bypass | CyberArk-owned product line |
| CVE-2026-0259 | 7.1 | MEDIUM | WildFire WF-500 | Arbitrary file read/delete | |
| CVE-2026-0243 | 7.1 | MEDIUM | Prisma SD-WAN | Denial of service | unauthenticated |
| CVE-2026-0239 | 7.1 | MEDIUM | Chronosphere Chronocollector | Information disclosure | third-party (Chronosphere) |
| CVE-2026-0256 | 6.9 | MEDIUM | PAN-OS | Stored XSS | admin-auth required |
| CVE-2026-0245 | 6.8 | MEDIUM | Prisma Access Agent | Information disclosure | |
| CVE-2026-0238 | 4.8 | LOW | Broker VM | Improper input validation | admin-auth required |
That gives us zero Critical, three High, twenty Medium, and one Low. The highest CVSS score in the AI-credited cohort is 9.2 for the three highs: an IKEv2 remote code execution flaw, a heap buffer overflow in DNS proxy and DNS server components, and a Cloud Authentication Service authentication bypass (see preconditions below).
Nine of the twenty-four include exploitability preconditions in the per-advisory Problem text:
- Authenticated administrator access required (3): CVE-2026-0261 command injection, CVE-2026-0256 stored XSS, CVE-2026-0238 Broker VM input validation
- Local privilege escalation against an attacker already on the endpoint (2): CVE-2026-0246, CVE-2026-0251
- Adversary-in-the-middle positioning against certificate validation (3): CVE-2026-0244, CVE-2026-0248, CVE-2026-0249
- Cloud Authentication Service enabled on a network-reachable management interface (1): CVE-2026-0265, a configuration the vendor’s own best-practice guidance has long advised against
These vulnerability classes are all very familiar to anyone with experience in static analysis tools running against a network appliance codebase. Buffer overflow in protocol parsers? Check. Certificate validation gaps? Check. Command injection behind administrator authentication? Check. Stored cross-site scripting in web consoles? Come on. Information disclosure in agent logs? Zzzzz. These findings are what commercial static analyzers like Coverity have produced against this product class for over twenty years. Palo Alto has written a post suggesting that the same-old same-old is suddenly a generational capability leap. But why?
The CyberArk Carve-out
The post explicitly excludes CyberArk vulnerabilities from the AI-credited count, on the grounds that CyberArk’s product security organization handles its own disclosure process. I guess I can go along with that carve-out. Except then I see three of the May 13 CVEs are issued against Trust Protection Foundation, the former Venafi product line that CyberArk acquired and that became part of Palo Alto Networks through the CyberArk acquisition:
- CVE-2026-0240, sensitive information disclosure
- CVE-2026-0241, multiple authorization bypass paths
- CVE-2026-0242, SQL injection
Each carries a Palo Alto-assigned CVE identifier inside the Palo Alto May 13 advisories. The exclusion claim and the headline figure just crashed into each other. If the exclusion is meant to be real, then an AI-credited total drops to twenty CVEs. And we have even less reason to believe the 26 claimed.
Non-AI Takes the Cake
Let’s just take a moment to also dwell on CVE-2026-0300, disclosed by Palo Alto eight days before the Defender’s Guide post. The advisory describes an unauthenticated buffer overflow in the User-ID Authentication Portal that allows a remote attacker to execute arbitrary code with root privileges on PA-Series and VM-Series firewalls. The User-ID Authentication Portal, also called the Captive Portal, maps IP addresses to authenticated user identities for traffic the firewall cannot otherwise attribute. By design it accepts connections from unauthenticated users at the network edge.
CISA added CVE-2026-0300 to the Known Exploited Vulnerabilities (KEV) catalog the following day. Federal civilian executive branch agencies operating under Binding Operational Directive 22-01 had until May 9 to remediate.
Unit 42 attributed the activity to a cluster designated CL-STA-1132 and characterized it as likely state-sponsored. Shodan identified approximately 225,000 internet-facing PAN-OS instances at the time of disclosure. The Unit 42 threat brief then records the first observed exploitation attempt against a Palo Alto device on April 9. Successful remote code execution followed approximately one week later. Project Glasswing launched on April 7. Is there any evidence at all that Mythos or any AI of any kind is to credit here? Palo Alto doesn’t seem to think so.
The patch for CVE-2026-0300 shipped on May 13, the same day Palo Alto published the Defender’s Guide claiming twenty-six AI-credited findings with none exploited in the wild. The CVE that drove the federal mandate was disclosed eight days earlier, attributed to attackers in production rather than to Mythos, and excluded from the twenty-six.
Think about it. We have seen this repeatedly since the Mythos FUD-balloon was launched. The most critical, most impressive finds have been reported by humans and not the Anthropic tools, inverting the headlines.
Cartel
Anthropic restricted Mythos to a vetted consortium of approximately forty enterprises on the grounds that its vulnerability discovery capability exceeded what general availability could safely support. The launch was accompanied by one hundred million dollars in Anthropic usage credits to participating organizations. On April 7, Treasury Secretary Scott Bessent and Federal Reserve Chair Jerome Powell convened an unannounced meeting at Treasury headquarters with the chief executives of the largest United States banks to discuss Mythos and the cyber risks it represents.
It read at the time like some kind of top-down business corruption, but we should all be patient to see if that’s what it really is.
The technical capability claim is the basis for the billionaire-consortium structure, the access restrictions, and the urgency framing that has since compressed from six to eighteen months in the April Defender’s Guide to three to five months in the May Defender’s Guide, with no methodology or science accompanying the contraction.
The first full month of Glasswing produced a Patch Wednesday batch consistent with what a competent static analysis pass produces against a network appliance codebase. It also produced a state-aligned remote code execution against the same product family that the AI scanner missed. The marketing text frames the first as evidence of generational defensive advantage. The second is disclosed eight days earlier and buried, even though it’s the one that counts the most.
The operational damage from the marketing trend is concerning.
Palo Alto customers reallocating budget on the basis of the urgency framing are moving spending away from operational basics like patch cadence, management interface segmentation, and captive portal exposure review, toward AI-flavored product spend that addresses a threat the cycle did not demonstrate.
I’m especially annoyed that Post Quantum is not getting sufficient attention these days.
The Defender’s Guide is so thick with “funnel” framing that it maps each recommendation to a Palo Alto SKU: Cortex Xpanse for attack surface management, Cortex XDR for endpoint detection, Prisma AIRS and the recently acquired Koi product for agentic endpoint security, Cortex XSIAM for the security operations center, and the new Unit 42 Frontier AI Defense service for the consulting tail. The SEC forward-looking-statements disclaimer at the bottom of the post gives away the true audience.
The institutional damage from the marketing trend is even more concerning.
The KEV catalog value to defenders depends on a listing being taken as the strongest available indicator of active exploitation at scale. The Defender’s Guide narrative depends on readers treating the May 5 disclosure and May 6 KEV listing as separable from the May 13 claim of a novel capability, that the evidence doesn’t support. On what real basis should Palo Alto depreciate the KEV signal?
Anthropic’s Glasswing has the substance of a marketing partnership. The model vendor restricts access to a vetted consortium. The consortium attests to the capability that justifies the restriction to the consortium. The model vendor pays the consortium one hundred million dollars in usage credits. The consortium sells the products that follow from the attestation.
Mozilla, and now Palo Alto, have only cemented the view that Mythos is not really what is being sold to the public.
Sources.
- Palo Alto Networks May 2026 Defender’s Guide: paloaltonetworks.com/blog/2026/05.
- April 2026 Defender’s Guide: paloaltonetworks.com/blog/2026/04.
- Primary advisory feed: security.paloaltonetworks.com/csv.
- CVE-2026-0300 advisory: security.paloaltonetworks.com/CVE-2026-0300.
- CVE-2026-0262 advisory: security.paloaltonetworks.com/CVE-2026-0262.
- Unit 42 threat brief: unit42.paloaltonetworks.com/captive-portal-zero-day.
- CISA KEV JSON feed: cisa.gov/sites/default/files/feeds/known_exploited_vulnerabilities.json.
- Rapid7 brief on CVE-2026-0300 (Shodan exposure figure): rapid7.com/blog.
- CNBC on April 7 Treasury meeting: cnbc.com.

Another very nice write up deflating the AI bubble. I also think quantum computing is the more interesting technology, and is not getting enough attention.
Though, I wonder about even when quantum computing will actually become viable. Here’s a very funny research paper showing that QC isn’t all that far along yet: https://eprint.iacr.org/2025/1237.pdf
The discrepancy you highlighted between the blog post claiming 26 CVEs and the authoritative CSV listing only 23 entries, plus the multiple 404s for specific CVEs, raises some real questions about the coordination process with other vendors. It’s a valuable reminder that published vulnerability counts can sometimes differ from the final official data until the full disclosure cycle is complete.