I’ve written here before about French use of encryption in the 16th Century, and prior art. A new history article makes brief mention of ancient secrecy methods found in England.
The spies had a few special tricks up their sleeves. “They practiced secret inks,” explains Alford. “Quite a lot of use of code and cypher, which to our eyes looks relatively unsophisticated, although it develops an increasing sophistication.” Cyphers became particularly important during the infamous Babington Plot, when Walsingham’s agents decrypted letters to and from Mary Queen of Scots. This provided evidence that Mary was conspiring against Elizabeth, leading to Mary’s trial and execution.
Provided evidence? Very important to understanding the fallout from the Babington Plot is that integrity was the bigger failure, on top of confidentiality being breached.
While in his possession, Walsingham had the letters deciphered and copied. In 1586, Babington wrote a letter outlining the details of the plot to rescue Mary. In the letter, Babington asked for Mary’s permission to assassinate Elizabeth. Mary responded and agreed with the plans, but did not authorized the assassination. That did not matter however, because Walsingham’s spies intercepted the letter. The letter was deciphered and copied but this time a postscript was added. According to the new letter, Mary authorized the assassination. Walsingham had his proof.
The proof was faked.
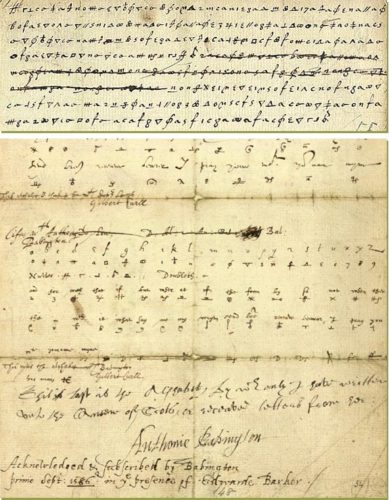
The UK National Archives have an example of the letters used (including the faked proof) and the Tudor Times explains the level of sophistication at the time
By the 1580s, ciphers were extremely complex – they could incorporate substitute letters, Arabic numerals, nulls, letters with a dot before or after, substitute names for locations, and numbers, signs of the zodiac or days of the week for individuals.
If you think that sounds innovative, consider how French and English secrecy methods seem to have roots elsewhere:
Muhammad ibn Abbad al-Mu’tamid (المعتمد بن عباد), King of Seville from 1069-1092, used birds in poetry for secret correspondence.
