Der Spiegel reports that Germany’s schools have learned to count antisemitism. Their April 24, 2026 edition draws a picture from a survey of the state education ministries.

- Hesse went from 39 reported far-right, antisemitic, and racist incidents in 2023 to 159 in 2025.
- Saxony rose from 149 to 247 over a comparable window.
- Lower Saxony climbed from 133 in 2022 to 322 in 2024.
- Across the nine states that gave figures, roughly 1,500 antisemitic and far-right incidents in 2024 alone, much of it banned symbols and graffiti.
- Saxony’s education minister, Conrad Clemens of the CDU, called right-wing extremism the single largest societal problem in his state’s schools.
As always, the figures have context that matters. The comparison windows do not line up. The ministries themselves claim, without data to back it up, that teacher sensitivity improved. Saxony’s separate count of all school reports to the authorities, from 55 in 2014 to 1,644 in 2024, is incidents reported. Where’s the proof that this has anything to do with better sensing? Most people say the opposite, that sensitivity to antisemitism is declining, which is why the acts have been increasing along with the AfD.
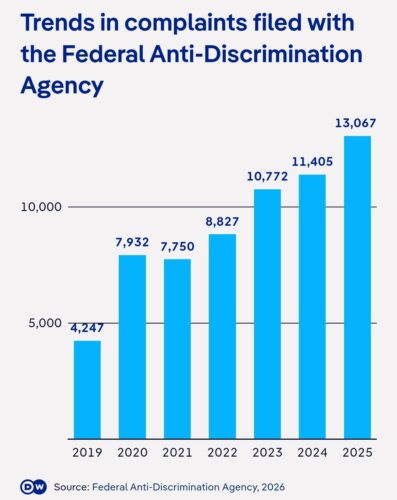
The 1,500 is a self-reported number with three states declining to answer. Declining to answer certainly doesn’t sound like improved sensitivity. The direction is not in doubt, and the most obvious apparatus is still the point: the German system can still see the swastika sprayed on the schoolyard wall as a bad thing, and is registering more every year.
What the German justice machinery cannot see
There is a particular thing this counting does not do, and it is because of how some of the worst antisemitism in Germany worked hard to normalize itself after 1945. It is in the music room.
A great many of these same schools teach music through a method that carries Carl Orff’s name. His name shouldn’t even be on it, given most of the work is Gunild Keetman’s and the framework beneath it is Leo Kestenberg’s. Putting Orff’s name on the cover is the least accurate thing about it, and the parents allow it typically because they claim no knowledge about Orff’s huge importance to Hitler. The spread of his name to children is because there remains no standardized curriculum. One of the largest figures in Nazi music arrives as though he were merely an introduction to the instruments, as if his face and name on the cover carried no more weight than any other pedagogy.
Carl Orff was forty-one and remained obscure as a composer when Hitler seized power. His full two decades of work had produced no breakthrough and he was unknown; this is partly why he himself dated the beginning of his real career as 1937, when he premiered Carmina Burana. His career began, according to him, four years after Dachau had been destroying opposition to Hitler, and on the doorstep of Kristallnacht and the Nazi invasion of neighboring countries.
The success came with and because of the Third Reich, and he secured it by courting the regime’s officials when he needed to and by using adherence to the Reich to overcome the regime’s conservative critics by winning the regime’s favor. He left the Nazi dictatorship with a high fixed income, high praise and official favor, and his highest honor of all the Nazi Gottbegnadeten exemption. The regime protected and rewarded him for serving it, at the same time it was executing men like his friend Kurt Huber, whom he refused to help.
After Hitler committed suicide he fraudulently told the Americans that the Nazis had disliked his music and that no Nazi critic had ever given him a good review. Both claims were patently false and easily disproved. Fritz Stege, a Nazi critic, reviewed him favorably. Orff had lied during the denazification process because it was based on whether he had been a beneficiary of the regime. Not only had he been a huge beneficiary, the openings he took existed only because Jewish musicians had been banned. Orff after 1945 even falsely claimed the valor of his dead friend Huber as his own. He lied repeatedly in many ways to launder his role in the Reich into a “grey” post-war curriculum work. And as a matter of fact, to his very last day he never, ever criticized Nazism or Hitler. Asked about it point blank, Orff wouldn’t condemn the Reich.
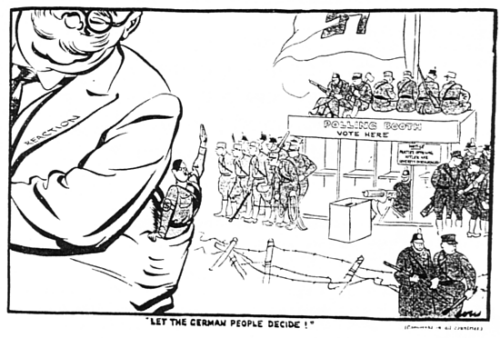
The ground he claimed and rose on, his career “success”, was made by force against Jews. When the regime wanted a score to replace Mendelssohn’s banned music for A Midsummer Night’s Dream, several composers turned the commission down. Werner Egk waved off a generous fee. Richard Strauss declined. Even Hans Pfitzner, an antisemite, refused, on the grounds that Mendelssohn’s original was better than anything he could have written. Orff took it. Schulwerk was set for trials in Berlin’s elementary schools in the early 1930s, arranged through Leo Kestenberg, the official in the Prussian education ministry who knew the method and could open the door. The trials never happened. Kestenberg, a Jew, was dismissed in 1933, and the door closed with him. Orff was an opportunist, which was worse than an ideologue, because the ideologue at least held values. Long after the ideologues were caught and stopped, Orff was still rising because he benefited from erasure of Kestenberg.
So here is the question Germany needs to start answering: wherever Orff is taught, does the swastika correlate? No registry tracks it. No ministry counts it. The people best placed to report it cannot, because they do not know how to classify the correlation of a Reich celebrity the children are being told to learn about.
The missing column
That absence of evidence is usually mistaken for evidence of absence. It is, instead, the evidence. A system that has assembled an elaborate apparatus to count antisemitic incidents has no field at all for the antisemitic history sitting inside its own music curriculum. It tallies the graffiti while it teaches the erasure of victims, and registers no contradiction, because the second item never enters the ledger. You cannot regress on a variable the institution refuses to admit let alone name.
Anyone saying Orff should not be removed from a wall, unlike the swastika, needs to answer for why only Orff is on that wall and not all the people removed so he could be there at all.
The numbers from the ministries describe a system straining to see what is sprayed on its walls. The thing it still teaches, the erasure of victims of the swastika, it does not see at all.
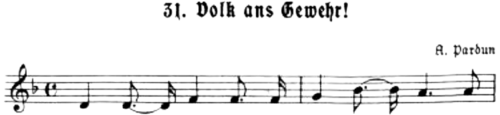
The 1936 work of Orff was offering an engine to the institutions that wanted it, and the same year the music-teachers’ own section of the NSLB printed Arno Pardun’s “Volk ans Gewehr” in a songbook for secondary schools, a song whose verses end on a call for death to the Jews.
To ignore all this is not a failure of measurement around the edges of the problem. The problem is Orff himself, promoted to children in Germany’s own schools with no mention that his success started with and because of Hitler, sitting unaudited.
Where a swastika gets painted, it is worth asking the music teachers how often, and where, Orff appears in their classrooms.