This is a timeline of proprietary and centralized end-to-end encryption technology (yes that is a contradiction, and yes it uses an open source protocol) for secret delivery of malicious content to targets (apps and people) that seems to have led to massive privacy loss as well as targeted killings.
January 2018:
Facebook’s CSO campaigned on Twitter to restore trust in WhatsApp after researchers alleged privacy flaws.
…clear notifications and multiple ways of checking who is in your group prevents silent eavesdropping. The content of messages sent in WhatsApp groups remain protected by end-to-end encryption.
March 2018:
Amazon CEO is invited to have dinner with the Saudi Crown Prince Mohammed bin Salman.
April 2018:
Amazon CEO and Crown Prince have dinner, exchange phone numbers linked to WhatsApp accounts.
May 2018:
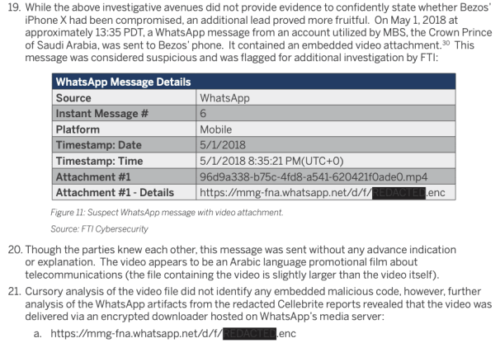
WhatsApp message from the Crown Prince (believed to have included a malicious video file) is sent end-to-end encrypted to the Amazon CEO’s phone.
A huge amount of data (130MB) suddenly is uploaded from the CEO’s phone (29,000% jump), and then about 100MB/day is uploaded in the months following (compared to under 0.5MB/day in months prior). (Full Report by “FTI Consulting” via Vice News story).
June 2018:
Amazon’s WashPo journalist Jamal Khashoggi’s contacts (who use WhatsApp) also receive malicious links.
July 2018:
NYT reports spread of harmful videos on WhatsApp is leading directly to dozens of violent deaths: “How WhatsApp Leads Mobs to Murder in India“.
WhatsApp’s design makes it easy to spread false information. Many messages are shared in groups, and when they are forwarded, [despite CSO promoting “multiple ways of checking who is in your group”] there is no indication of their origin.
August 2018:
Facebook CSO leaves to take position at Stanford doing research for Facebook, pushing for greater use of WhatsApp (see Oct 2019 Stanford tweet).
…companies like to say things like ‘we follow local law’, but in reality, they resist orders every day by saying ‘sorry…
His statements promoting WhatsApp usage completely contradict his infamously bizarre 2015 argument with the NSA (just before being hired by Facebook), which suggested he saw moral equivalence in all lawful orders from everywhere.
…if we’re going to build defects/backdoors or golden master keys for the US government, do you believe we should do so — we have about 1.3 billion users around the world — should we do for the Chinese government, the Russian government, the Saudi Arabian government, the Israeli government, the French government? Which of those countries should we give backdoors to?
Facebook CSO publishes his own Wikipedia page full of uncritical self-promotion and demands it be locked to prevent the public from editing or commenting.
I’ll try to keep an eye on this page for any questions.
September 2018:
Amazon CEO’s phone uploads 500MB.
October 2018:
Khashoggi is murdered at the Saudi consulate in Istanbul.
Slate reports on spread of harmful content on WhatsApp, describing it as dangerous tool for mob rule and abuse of power: “How False News Haunted the Brazilian Elections…it was worse than ever.”
And it coincided with the rise of Brazil’s far-right president-elect…political communication is completely vulnerable, especially on WhatsApp because it’s not monitorable… Just 8 percent of the most-shared information in groups was correct… WhatsApp, which she described as “the biggest misinformation engine during elections this year”, was unwilling to take action against fake news on its platform. …the company “at no point showed itself willing to sit down and talk with fact-checkers to think about solutions.”
November 2018:
US White House occupant reportedly in a “bizarre, inaccurate and rambling” manner “issued a statement in which he said the U.S. would maintain a ‘steadfast’ alliance with Saudi Arabia, refusing to blame Saudi Crown Prince Mohammed bin Salman for Khashoggi’s killing even though the CIA has reportedly concluded that the crown prince ordered his assassination.”
March 2019:
US Congress sends letter criticizing WhatsApp being used in White House for communications with foreign leaders during September and October of 2018 (murder of WashPo journalist).
April 2019:
Ex-Facebook CSO gives talk with huge privacy claims (without any evidence) while Amazon CEO’s phone is uploading GB of extremely sensitive data due to security flaw in WhatsApp; self-congratulatory boasts of the ex-CSO go unchallenged.
CISOs comment about Stamos in private executive forums (sorry can’t disclose sources): “That boy loves a microphone and a camera, but those can’t keep your systems from crashing.”
April/May 2019:
Amazon CEO’s phone completes 9GB of data uploaded in three large bursts.
12 days after last burst, a full forensics investigation begins by FTI. While unable to find malware FTI writes report showing bursts of suspicious traffic.
November 2019:
Facebook announces CVE-2019-11931, which explains sending a malicious video file to a WhatsApp user has been a serious open vulnerability allowing spyware to be installed. May 2018 to November 2019 is 1.5 year response time to a critical exploit in the wild.
Description: A stack-based buffer overflow could be triggered in WhatsApp by sending a specially crafted MP4 file to a WhatsApp user. The issue was present in parsing the elementary stream metadata of an MP4 file and could result in a DoS or RCE. This affects Android versions prior to 2.19.274 [OCT 3, 2019], iOS versions prior to 2.19.100 [OCT 17, 2019]….
January 2020:
Guardian breaks the story of Amazon CEO and Whatsapp breach, barely hinting at a US White House role.
[In high-profile and long-standing “challenge” to Amazon CEO] Trump and his son-in-law Jared Kushner have maintained close ties with the crown prince…
Further stories roll like NYT “Beware WhatsApp accounts…”, which bring us full circle to the Facebook CSO making a provably false claim in public that “clear notifications and multiple ways of checking who is in your group prevents silent eavesdropping”.
To be clear the phrase “prevents silent eavesdropping” was a very tall claim that deceptively lured victims to false sense of trust in WhatsApp. Eavesdropping wasn’t prevented entirely, and harmful content wasn’t even attempted to be prevented, so many people died as a result of overconfidence from WhatsApp marketing coupled with its critical security flaws.
Related:
WhatsApp CVE-2021-24026 allowed complete system compromise due to a missing bounds check within the audio decoding pipeline for calls.
WhatsApp CVE-2019-18426 allowed attackers to read files from users’ local file systems.
WhatsApp CVE-2018-6344 allowed attackers to fully compromise the app when a target answered a call.
November 1997, Microsoft IE 4.0 browser buffer overflow allowed attackers to “execute arbitrary precompiled native code” (i.e. F00F of concept would denial-of-service the Intel CPU).