It’s pretty clear from a series of rapid and unfortunate missteps by Zoom that there’s something fundamentally wrong with the company. This is way worse that what I was warning about here in 2007.
We already knew the origin story didn’t sound great.
A VP of Engineering at WebEx, after being acquired by Cisco, didn’t like working for the parent company and left to start a direct competitor to move faster. The new company was basically the Chinese engineers rejecting their American parent company. The revolt even was funded by one of the WebEx founders who used the same money acquired from Cisco to compete with Cisco.
…he knew how to write computer code, and he landed an engineering job with the videoconferencing software company WebEx. WebEx sold to Cisco for $3.2 billion a decade later (the platform is now known as Cisco Webex). Yuan became the tech giant’s vice president of engineering, earning compensation in the “very high six-figures.” But he was unhappy. […] In Yuan’s opinion, the product didn’t evolve quickly enough, making it a chore for customers to use. (In fact, Yuan told CNBC earlier this year that Cisco was still using the same buggy code he wrote for WebEx roughly two decades ago.)
The article goes on to say that claim by Yuan about the WebEx code is false, a lie.
…senior vice president and general manager of Cisco’s team collaboration group, says the company has “redesigned Webex from the ground up” since Yuan’s tenure…
It’s very weird for Zoom’s CEO to suggest WebEx is bad code because his team of Chinese engineers wrote it. Does that make you want to use his new product founded by the same team when he’s shaming his old product? I mean it really opens the door to people (like me) pointing out this guy is willfully allowing bad code into production because that’s “his way” of doing things. He literally poached the WebEx engineering team to compete directly with WebEx, while calling the WebEx code buggy.
For the first two years of Zoom’s history, the company was just a small team – mostly engineers from WebEx [in China].
Is it time yet to use one of the safer alternatives to Zoom?
Clearly something seems off kilter in Zoom executive management ethics related to product safety. Security appears to have been treated as a non-feature and afterthought. Just look at these recent examples:
- Zoom security flaw exposes email addresses, full names and profile photos, as well as allowing non-invited attendees to initiate a chat
- Zoom security flaws in OSX allow (local) installer priv-esc vulnerability to root, (local) injection flaw allowing access to mic & camera
- Zoom security flaws of weak encryption and suspicious key traffic to China
- Zoom security flaw of disclosing Windows user passwords and local file execution
- Zoom security flaw in meeting identification facilitated unauthorized access
- Zoom security flaw allows any website to enable your camera without your permission
- Zoom security flaw allowed unauthorized command execution on Windows, Mac and Linux
- Zoom security architecture allows interception of traffic, opposite of marketing materials claiming end-to-end encryption
- Zoom weak security default left private recordings exposed to the public
- Zoom secretly was recording user information without authorization
- Zoom secretly was recording device information without authorization and forwarding to Facebook
- …and the list goes on and on.
I’ll stop to point out, perhaps for those who haven’t worked in product security, that this kind of “scientists crapping all over Zoom” list (also known as audit findings) is exactly the kind of pressure that helps an internal team fight more effectively for safety fixes earlier in the development lifecycle.
For example, an independent cryptography analysis (see also my explanation here) has found this:
Zoom documentation claims that the app uses “AES-256” encryption for meetings where possible. However, we find that in each Zoom meeting, a single AES-128 key is used in ECB mode by all participants to encrypt and decrypt audio and video.
How is that not just straight up deceptive practices and delivering a known unsafe product to market? The centralized management of a single key by Zoom, and decryption capability of meeting traffic by Zoom, violates both the spirit and letter of end-to-end encryption.
And if I understand the Zoom architecture correctly, any time someone uses a mobile device to dial into a video chat (which is basically all the time) Zoom is decrypting the meeting on their servers. The very thing that Zoom’s CEO said he started a new company to solve, by moving faster than he was allowed to at WebEx, is this mobile device compatibility architecture decision that undermines privacy while deceptively marketing it as safe.
And on top of weak key management, that key is routed through China even when nobody in a meeting is in China. Apparently 80% of Zoom 2019 revenues were from China, and just last September that country said Zoom traffic had to route through servers based in China or Zoom would be blocked completely.
When researchers asked why traffic from the US was routed through China, however, the CEO tried to play dumb and said it must have been a mistake.
With this kind of obviously compromised decision-making, deceiving customers about encryption (calling it end-to-end when it is not), it brings front and center the fact that Zoom has issued no transparency report (PDF) about who is in fact getting access to the data.
A lack of transparency about access to internal data, coupled with a lack of leadership integrity and pressure to force it, allowed Zoom to run far afoul of basic security principles.
New transparency from researchers is bringing external pressure that should have been applied internally all along. One can hope late is better than never, yet experience suggests all these flaws are mere symptoms.
Zoom has said they will now stop feature development to focus on privacy, which is just another symptom. Remember the CEO comment about WebEx running his buggy code? He went into this knowing right from wrong and developed code the wrong way anyway. Privacy is a feature just like usability, so to see it called something that stops feature development… is part of a wider leadership ethics problem.
It goes back to that questionable origin story. A company was founded on impatience and greed (masked as usability from highly responsive user-focused engineering), which typically doesn’t mix well with safety values.
Making “Zoom bombing” a crime may help dissuade some abusers taking advantage of the safety weaknesses inherent to Zoom. However, that doesn’t fix the problem of Zoom itself being an untrusted company.
Right now shifting to a different product may be the easiest and most secure measure relative to Zoom’s problems. Consider the many options that may be in a better position right now, including of course WebEx. Here are links to their trust team and/or privacy policies:
- Cisco WebEx (3 women on board of directors)
- Savoir-faire GNU Jami (core committers not found)
- 8×8 Jitsi (2 women on board of directors) and further details on their communications page
- BigBlueButton (0 women in core committers)
- BlueJeans (0 women on board of directors)
- LogMeIn GoToMeeting or Join.me (2 women on board of directors)
- Avaya Spaces (2 women on board of directors)
- Microsoft Teams and Skype (3 women on board of directors)
- Apple Facetime (2 women on board of directors)
- Google Meet (2 women on board of directors)
- Wire (0 women listed in management, 4 claimed as “step-up leaders”)
- Wickr Pro (0 women listed in management)
- Whereby (woman founder)
One of the most interesting options is Jitsi because it is open source (like Jami and BigBlueButton) and allows you to run your own server for meetings. While true end-to-end encryption is difficult to implement given the nature of video conferencing protocols and features, moving to a hosted server means you can have more confidence that any necessary decryption is done within a trusted zone.
Also a quick caveat about Zoom’s buggy code because it found its way into the hands of a lot of people. Here are some of the major brands who run it under the covers and also tend to be vulnerable to security mismanagement and exploits:
RingCentral, Telus Meetings, BT Cloud Phone Meetings, Office Suite HD Meeting, AT&T Video Meetings, BizConf, Huihui, UMeeting, Zhumu, Zoom CN, EarthLink Meeting Room, Video Conferencia Telmex, & Accession Meeting
Beware what’s under the covers of your video conferencing system.
Update April 6: a serious security issue was just reported in Jitsi: https://github.com/jitsi/jitsi-meet/issues/5720
TL;DR – meeting password protection can be bypassed by simply showing up in a meeting room before the host arrives
A benefit of open source over proprietary projects is how security flaws like this can be so easily raised and monitored.
That being said, this is a pretty awful bug. No software is devoid of flaws so it really comes down to how this entered the product (e.g. how symptomatic is it of wider issues), how the response goes and how it is communicated.
More details on this in terms of Zoom handling flaws, in comparison to WebEx, is in a new post.
Update April 22: Jitsi has announced an update to end-to-end encryption. Their security page already was very clear about privacy modes, risks and trade-offs. Now it’s been updated.
Thanks to the insertable stream API, that recently landed in Chrome Canary, Jitsi Meet is now able to manipulate encoded packets before sending them on the network, and as a result we have been able to launch our new efforts on end-to-end encryption. Check out the demo and our next steps here: https://jitsi.org/e2ee
Great news and I appreciate it was announced on availability!
Update May 7: Zoom has blasted the news cycles with a pre-announcement a future release of some encryption that may happen someday. This is garbage. The company being acquired says:
Initially, our single top priority is helping to make Zoom even more secure. There are no specific plans…and we’ll see where that takes us.
Zoom admits it won’t have much of an impact, assuming it even happens, and it backpedals in its own announcement describing the desire for privacy as a loss.
…for hosts who seek to prioritize privacy over compatibility, we will create a new solution… for paid accounts… end-to-end encrypted meetings will not support phone bridges, cloud recording, or non-Zoom conference room systems.
In other words, people who pay for accounts so they can have things like bridges, recordings and room systems won’t benefit from the new solution that’s being designed for paid accounts alone to use.
Zoom hates privacy and uses these deceptive fluffy pre-announcements to fool people. Don’t use Zoom.
Update May 12: on a typical day I’ll be asked to connect on a half dozen video conferencing platforms. Everyone seems to prefer their own. This seems fine, although a standard that all the clients could interoperate on would be better.
Anyway, out of them all I’m seeing a trend in the most highly aware security and privacy groups to invite me to Whereby meetings.
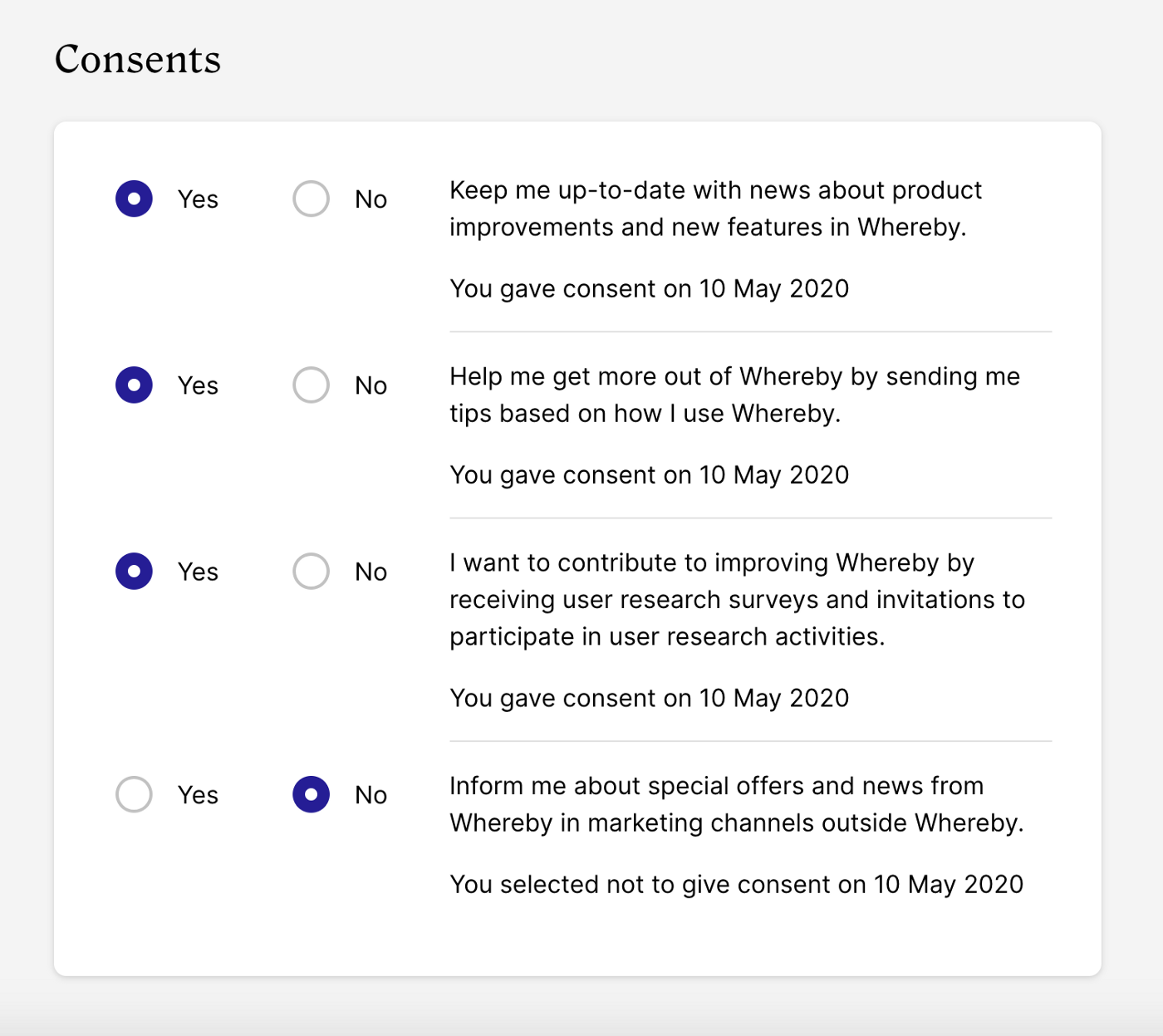
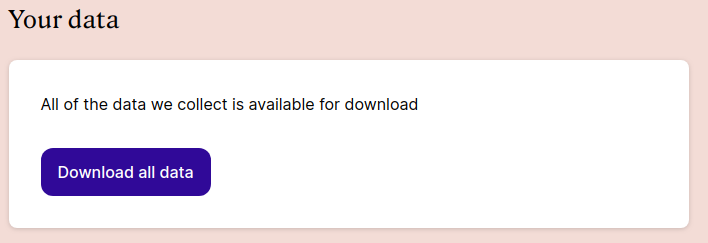
Besides being a fantastic user experience, the very clear and simple Whereby privacy site makes it easy to see why it has become a leader.
This is excellent stuff: