The old joke was that putting fingerprint readers on devices meant people would get their hands cut off, or at least they’d be drugged to use their hands without consent.
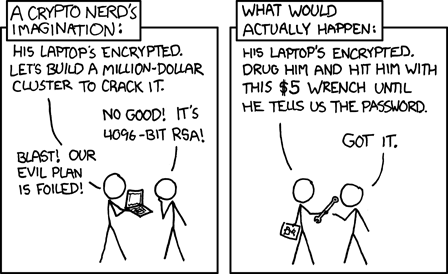
Of course we haven’t heard much about such “rubber hose” attacks, even as fingerprint readers have been put into practice everywhere on everything. The best real world threat so far, perhaps, has been “gummy bear” integrity attacks a decade ago.
A new research paper tries to bring sensor security back into focus by demonstrating a simple brute force method, which only seems to work on Android phones due to… Google’s infamously low security bar.
An attacker is meant to take a fingerprint database — given open research or centralized collection resulting in inevitable giant leaks — with about $20 in hardware, to quickly brute force any Android device.
Because fingerprints are generally low integrity to start with, researchers point out how they benefited from using a simple manipulation of “false acceptance rate” (FAR). That’s as bad as it sounds. Your safety depends on an adjustable acceptance rate of bad authentication. How many bad attempts would you like to treat as good ones? In addition, they mention how the serial peripheral interface (SPI) on Android can be compromised to leak fingerprints (while iOS by comparison reasonably encrypts the SPI).
When just one fingerprint is enrolled the researchers estimate 3-14 hours to brute force their way through. When more than one fingerprint is in the SPI, their estimate is only 1/2 to 3 hours to force a collision!
∀F(Fx ↔ Fy) → x=y
The big question becomes whether fingerprint gathering methods to produce a specialized database (e.g. things thrown into the trash by targets), instead of generalized prints, would reduce times even more dramatically. Then again with this 1/2 hour rating given $20 tools, why bother?
