Raise your bloodied hand missing fingers if you lived through SHA-1 deprecation. What about 3DES?
For those who don’t remember, Xiaoyun Wang, Yiqun Lisa Yin & Hongbo Yu published the collision attack in 2005. Google’s ad-revenue funded deep bench of engineers produced a working collision in 2017. The twelve miserable years between them were filled with noise about why the sunset timeline was unrealistic. Standards bodies ran interop events that nobody implemented, and CAs kept selling SHA-1 certs until the registrars stopped taking them. Banks, proving the old adage that privilege and power make you stupid, kept shipping SHA-1 internal certs long into 2019.
The cryptanalysts were not wrong. The institutions were not on time, because they aren’t funded by advertising and so they have to mind actual margins. The margin managers push back on deadlines because pushing back is cheaper than protecting customers.
Fun fact, PCI DSS has always been about payment card brands whacking banks with a huge stick to get them to upgrade consumer safety. 2016 was the absolute deadline for TLS v1.0 deprecation and banks cried a tidal wave that pushed it back all the way to 2018. Bad for you, bad for me, good for bank margins.
Anyway, my beard is grey enough already. Let’s talk about today. The same pattern is playing out again, only the deadlines are shorter and the damage is worse. The cryptanalysts are publishing. The institutions are dragging. The vendors are hedging. Pour one out to my colleagues already six feet under, who no longer have the pleasure of rotating keys.
Filippo Valsorda is the bellwether. Two years ago he was the guy telling everyone to ship Kyber hybrids. This month he is telling everyone to skip hybrid signatures. Done. Dusted. Your window closed.
It’s pure ML-DSA-44 or nothing.
Today I’m here to tell you that anything still negotiating classical-only key exchange in 2026 should from this point forward be treated as a potential active compromise. I am not saying “future risk.” This isn’t “areas for improvement.”
Active. Compromise.
As in, assume someone is sitting in your traffic right now and is going to read it later like you didn’t protect it, because you didn’t.
The reason hybrid signatures just blew up is the vendors invested in the wrong insurance. Eighteen composite key types in the IETF draft. Sixteen revisions of the spec already, with another year of revisions to come. Wire format negotiation. Certificate chain handling. Years of vendor work, then years of operator work, all to hedge against the possibility that ML-DSA gets classically broken before the quantum computers arrive.
It’s an interesting game. Watching the world’s best cryptanalysts beating on ML-DSA for eight years has produced nothing. It is still running like a champ. The hedge is looking more and more like a gamble that failed.
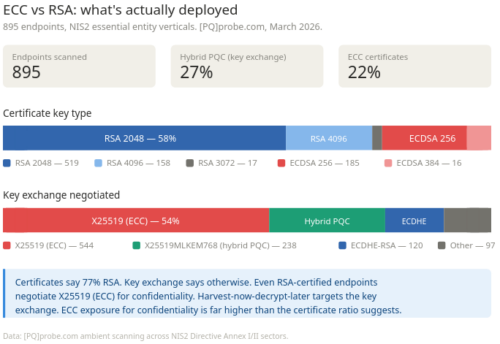
Meanwhile classical key exchange is cooked. Stick a fork in it. I’ve been warning CISOs on hundreds of calls for the last year that 2027 would be a shitshow if they didn’t get prepared for what’s coming. Google’s internal PQ deadline now is officially 2029. We’re looking at a fuse just 33 months long. Google Quantum AI published in March that the resources to break secp256k1 fit under 500,000 physical qubits with runtime measured in minutes. The Chevignard, Fouque, and Schrottenloher paper at EUROCRYPT 2026 cut the logical qubit count for breaking P-256 nearly in half, from 2,124 down to 1,193. The numbers that mattered six months ago no longer apply. ECC breaks first because its smaller keys need fewer qubits. RSA breaks second. The most exposed thing on your network is your modern X25519/ECDSA stack, not some legacy RSA box gathering dust bunnies in the corner. OpenSSH put a warning on non-PQ key agreement in the last release, the same way they warn on self-signed certs and weak passwords.
That’s actual real-world urgency.
The German BSI requires hybrid for both KEX and signatures. The French ANSSI requires hybrid for both. And the American NIST is somewhere in the middle, slow-walking a hybrid mandate while industry lobbying keeps it stuck in voluntary guidance. The Anthropic cartel is leading that effort.
I’m reading an IETF draft 16 of the composite signatures spec while the engineer who built the original Kyber hybrids is saying forget it. Too late. Wrap it up.
This sucks for those of us trying to run an operation because every scanner will grade the same TLS endpoint differently depending on which way an authority blows.
Welcome back to the stupidity of the SHA-1 transition, only with deadlines shaved down six years and consequences a lot worse than a forged certificate. The breach already happened. Someone is soaking up your traffic now. They read it when their qubits arrive.
I wrote some of this up in plain mode on [PQ]probe so you can share it at work:
The hybrid signature split: Filippo Valsorda has reversed his position on hybrid signatures: pure ML-DSA-44 is fine for sigs, hybrid stays for KEX, non-PQ KEX is a potential active compromise. The shift puts BSI’s hybrid mandate and the new Geomys/OpenSSH posture on a collision course. Scanners will need to report against both.
Three things to do this week. Drop classical-only key exchange yesterday. Ship X25519MLKEM768 hybrid for KEX. Ship pure ML-DSA-44 for signatures. Change pants.
Sorry, four things.
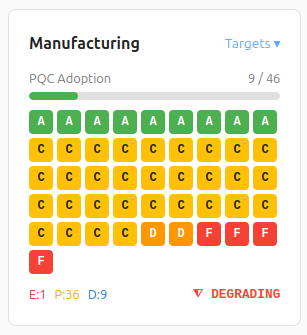
Since your remaining 33 months are going to be half that by the time budget approval stops fixating on AI nonsense, I made [PQ]probe as comprehensive, cheap and easy as possible. Mind the handshake size change. You can use our PQ calculator to see what hits the wire.

Grab your probe, get on 44 now or get cracked.
