Eleven days into the bombing of Iran, the United States has struck over 3,000 targets, killed the Supreme Leader, destroyed the state broadcaster’s headquarters, hit a parliament building, bombed a girls’ school full of children, mined the news cycle with claims of victory, and accomplished exactly nothing that wasn’t predictable, reversible, or counterproductive.
American “force projection” officially is degraded.
Iran elected a new Supreme Leader in eight days, while Trump said they weren’t allowed to do that. Its missile launch rate dropped 90% according to the Pentagon, which sounds decisive until you notice that the remaining 10% has still killed eight American service members, injured 140 more, struck US bases across the Gulf, hit civilian targets in Israel, shut down the Strait of Hormuz, grounded all flights out of Qatar, and turned every Gulf state hosting American forces into a target. The 90% number is a tactical metric being presented as a strategic outcome. It is neither.
American “dominance of the skies” officially is degraded.
There’s no denying drones are getting through. There’s no turning back that three F-15E fighters were shot-down by America’s own “dominance” system. The world learns to just watch and wait as “punch down” war criminals like Hegseth are sucking oxygen out of American state podiums.
הקונספציה (The Conception)
Trump unilaterally waded into the most predicted war in modern history. Not predicted as in “analysts warned it could happen.” Predicted as in the specific sequence of provocation escalation, failed negotiations, Israeli strikes, US involvement, Iranian retaliation against Gulf states, Strait of Hormuz closure, coalition fragmentation was ALL described in writing by dozens of analysts, think tanks, war games, and intelligence assessments over the past two decades.
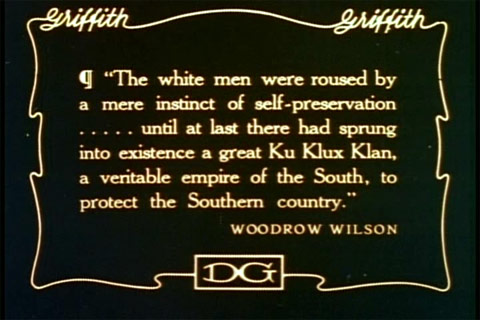
MAGA literally means go back to the days before we had so much intelligence to do the dumbest things possible, as if it will turn out differently by pretending nothing has been learned.
The Millennium Challenge 2002 war game simulated a US-Iran conflict and the red team sank a carrier group on the first day using exactly the kind of asymmetric tactics Iran is now employing. The Pentagon’s response was to restart the exercise with rules that prevented the red team from winning.
That was twenty-four years ago. The institutional response to being told the strategy would fail has been, for twenty-four years, to adjust the simulation until the strategy succeeds on paper. And then Trump came along.
קו בר-לב (The Bar Lev Line)
I wrote twelve years ago a detailed analysis of President Nixon’s folly called Operation Igloo White. And I’ve given many presentations about it since.

The billion-dollar-a-year sensor-to-shooter network the US Air Force dropped along the Ho Chi Minh Trail from 1967 to 1973. Twenty thousand sensors, relay drones, IBM mainframes, precision airstrikes. It cost $30 million in orbiting aircraft and command infrastructure to hit $5,000 trucks carrying $2,000 worth of rice. The programme ran for six years.
Bombs kept dropping, illegally, yet logistics kept flowing.
The Iran campaign is the Big Tech debacle of Igloo White at national scale. The most expensive precision strike capability in history directed at an adversary who has designed their systems to absorb exactly this kind of punishment and grow in capabilities. The IRGC operates with pre-delegated launch authority. Missile units are dispersed. Drone production is distributed across the country. The leadership succession mechanism activated within hours of Khamenei’s death. The system was designed to survive decapitation because the Iranians spent forty years watching what the US does to centralized command structures.
The US strategy assumes the adversary doesn’t learn or listen and remains conveniently fragile. I can’t believe I’m seeing the Vietnam War strategic failures made again as if none of it mattered to American brass. The adversary is not fragile. The adversary read the history and so this becomes a question of who follows a curve in the road ahead to slowly cross a chasm and who has a case of mode confusion (drives high speed forward off the side of a bridge).
טוהר הנשק (Purity of Arms)
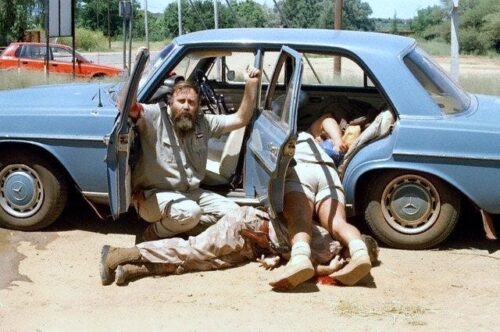
On the first day, the Shajareh Tayyebeh girls’ school in Minab was double-tapped by US missiles. At least 180 people were killed, rising by the day, most of them girls aged seven to twelve.
The school had been walled off from an adjacent IRGC naval base for over a decade, since 2013. That separation is clearly visible in commercial satellite imagery for that whole decade. NPR’s analysis, confirmed by three independent experts, assessed the strike as part of a precision attack on the adjacent military complex using targeting data that was never updated, did not reflect a school’s clear separation from an old base.
Red Crescent medics reported the double-tap mechanism used: after the first strike, the principal moved surviving students to a prayer hall and called parents. The second strike is what killed the children as it hit them sheltering in a prayer hall. Minab’s mayor says the school was struck three times.
Trump tried to push obvious propaganda, diminishing himself and America, by claiming without any reason or evidence that Iran bombed itself. Meanwhile the video geolocated by Bellingcat shows a cruise missile striking the compound, which an independent weapons expert assessed as inconsistent with any known Iranian-made design. Is anyone surprised that Trump is out of touch with basic reality, covering up his role in systemic harm to little girls?
Sixty-nine children’s remains are still being identified by DNA.
This is a known deadly military coordination gap. Many of us are steeped in the logic, as it killed forty-two people at the MSF hospital in Kunduz in 2015. The information that should have prevented the strike existed in a system somewhere. It did not reach the person who pushed the button. Consider how Palantir feeds this as a for-profit slop system that sponges money even as it becomes less accurate, proliferating the exact threats that it bills itself as targeting.
At Kunduz, the hospital’s coordinates were in the database but not in the fires chain. The purple hat Palantir incident was an intelligence analyst who proved the software deeply flawed compared to what was in his head. At Minab, the school’s separation from the base was visible to everyone from the ground and from space but apparently not to those operating the American target set.
At Kunduz, the US apologised, investigated, paid compensation. At Minab, the President of the United States said the Iranians did it to themselves.
מיצרי טיראן (The Straits of Tiran)
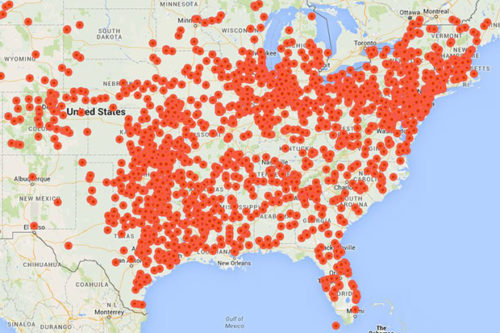
Iran is predictably laying mines in the Strait of Hormuz. One-fifth of the world’s crude oil transits the strait. Trump wants people to know only a “few dozen” mines have been laid so far, and sixteen mine layers are sunk, but Iran retains over 80% of its small boats and minelayers and an estimated 2,000 to 6,000 mines in stock. The opening move is not the end of a campaign.
The strait remains functionally closed. Tanker operators are refusing to transit. Supertanker costs have hit record highs. Major marine war risk providers have scrapped cover for vessels in the Persian Gulf. Qatar has grounded all commercial aviation. Insurance markets have repriced the entire Gulf.
Trump ordered the Navy to escort tankers through the strait. The Navy is refusing “near-daily” escort requests from shipping companies, saying risks are too high. The president is writing checks the Navy won’t cash.
Here’s the truth about Trump: in late 2025 he decommissioned the four Avenger-class minesweepers stationed in Bahrain. He cut the ships specifically designed for this mission. Their replacements, Independence-class littoral combat ships, cannot do the job. Naval News assessed them as unable to meet operational mine countermeasures requirements.
Trump removed the tool, then announced he would solve the problem he created, with no way to deliver.
America tripped over Trump clown shoes into the asymmetric response that every war game predicted and every policy maker ignored. Iran cannot match US air power. It was never going to try. It was always going to attack the coalition’s economic logistics because that is the thing the coalition cannot live without and cannot defend everywhere simultaneously. The Gulf states who were told this war would be quick and contained are now absorbing Iranian strikes on their oil facilities, their ports, their airports, and their civilian populations because they host the degraded and confused American forces.
The coalition fragments as the costs are falling on countries dragged into this war. Spain denied basing rights and got repeatedly bashed and threatened by Trump. Kuwait infamously destroyed a 50 year F-15E combat record by downing three in one night with friendly fire. Bahrain is taking missile strikes on its naval facilities. Qatar suspended Ramadan public gatherings. This is what happens when the strategy assumes a Nazi-blitzkrieg doctrine will somehow work today even though it lost everything in WWII. American popular opinion started low and is only going down, a pain threshold already reached, while the adversary does not collapse.
אין ברירה (No Choice)
Trump says he’s ahead of schedule every week, like how Elon Musk promised driverless cars nationwide by 2017 and landing on Mars by 2018. These pathological liars will say four to five weeks, a couple months, by the end of the year, about anything. The Iranians say they’re prepared for a long war and have a very long record of making it happen. The arithmetic is straightforward.
The US is expending precision-guided munitions at a rate that is not sustainable. Hegseth has publicly admitted he can’t keep it up. The stockpile problem that emerged in Ukraine, where production rates couldn’t keep pace with consumption, applies here for a larger target set and a faster tempo. Tomahawks are roughly $2 million each. The US has fired hundreds as if this is the most important war in its history, blowing everything at once. The replenishment pipeline is being measured in years, not weeks.
Iran’s expensive assets like ballistic missiles, launchers, and air defenses are depleting as expected. Meanwhile its cheap assets of naval mines, commercial drones, proxy networks, and the simple geographic fact of the Strait of Hormuz are either inexhaustible or irrelevant to destroy. America cannot bomb a strait open. America cannot precision-strike a mine that hasn’t been laid yet. America cannot destroy the idea that Gulf oil infrastructure is targetable when every tanker operator on earth has just watched it get targeted.
The US strategy requires Iran to capitulate before the coalition’s costs overflow and willingness to pay ends. Hegseth refusing to publicly discuss even the first six dead soldiers, and then Trump refusing to honor them, speaks to just how weak the administration is already. Iran’s strategy requires the coalition to fracture before Iran’s military capacity is fully degraded. The difference is that one side defined its breaking point before the war started (decades of planning a quagmire), and the other side assumed the breaking point wouldn’t matter because the media cycle could be saturated faster than casualties could be buried without recognition or respect.
This is the definition of a forever war. Not a war that lasts forever, but a war that lasts longer than the media-controlled strategy assumed, fought at costs higher than the strategy budgeted, against an adversary more resilient than the strategy modeled, producing outcomes more destabilizing than the strategy predicted.
שלום הגליל (Peace for Galilee)
The US keeps resetting its objectives to avoid being called out on them: degrade Iran’s nuclear programme, destroy its missile capability, induce regime change. Eleven days in, the nuclear facilities have been struck but Iran’s enrichment knowledge cannot be bombed. The missile capability has been degraded but not eliminated, and the asymmetric alternatives have not been touched. The regime changed when Khamenei’s son replaced his father in eight days, and the IRGC pledged allegiance, where the institutional structure continued without interruption.
The definition of success keeps shifting to avoid being held accountable, like how Tesla and SpaceX juiced Wall Street for a decade while failing to reach objectives. First it was “degrade and deter.” Then it was regime change. Netanyahu addressed the Iranian people in Farsi and told them to take to the streets. They came out to mourn the 180 little girls bombed in Minab and rally behind their government. Some still protested, as they had in January before the bombs started falling. The bombing failed to create a unified opposition. Instead it appears to have created a more unified country.
Daniel Levy, former Israeli government adviser, told Al Jazeera that Israel has “no real interest in smooth regime change” and is more interested in the principle of neighboring state collapse — Iran imploding, with the spillover destabilising Iraq, the Gulf, and the region. If that’s the actual objective, like how apartheid operated with South Africa destabilizing its neighbor states, then the strategy is working exactly as designed. It’s just not the strategy anyone sold to Congress, to the Gulf allies, or to the American public.
המצב (The Situation)
Iraq, 2003: shock and awe, decapitation strikes, mission accomplished, twenty years of occupation and insurgency.
Libya, 2011: air campaign, regime change, state collapse, a decade of civil war and migrant crisis.
Afghanistan, 2001-2021: the longest war in American history, ended with the Taliban back in power.
In every case, and I could go back even more years, the air campaign succeeded tactically and the strategy failed because it assumed that destroying the adversary’s visible military capacity would produce a political outcome it could not produce.
Iran is not Iraq, Libya, or Afghanistan. It is larger, more industrialised, more geographically defensible, and its population is more unified by external attack than divided by internal grievance. The assumption that this time a complicated strategy will work because the understanding is simplified with terms like “precision” is not a strategy. It repeats the exact mistake of Korea and Vietnam. Remember why Davy Crockett M-28/M-29 and Tarzon VB-13 were non-starters? We are witnessing prayers and wishes heavily inflated to a $2 million price tag per unit.
So the forever war everyone predicted is hard to deny this week, and looks like it only will get worse. The question was never what would happen. The question was always how long it would take for the people who started it to admit that the strategy they were sold is the same strategy that has failed every time it has been tried, at every scale, against every adversary that was prepared to absorb the punishment and wait.
The Ho Chi Minh Trail sustained logistics through six years of the most expensive sensor-to-shooter network ever deployed. Those who study, know. Iran has been preparing forty years for this moment. The question is not whether American precision munitions can choose Iranian targets and report narrow mission accomplished repeatedly. They obviously can. The question is whether destroying any of these targets produces any actual outcome the strategy requires. The answer, eleven days in, is the same answer it was on the Ho Chi Minh Trail, and in Iraq, and in Libya, and in Afghanistan.
No.