Update February 2024:
“X Twitter Keeps Promoting Slavery. It’s No Accident.”
Not very surprising, but very late. This should have happened years ago.
Gerber, who held some 420,000 shares of Tesla stock as recently as this spring and is the CEO of Gerber Kawasaki Wealth and Investment Management, said his clients are “pissed off.”
“Getting a flood of messages from clients wanting out of Tesla and anything to do with Elon Musk,” he wrote on X. “Many saying they are selling their cars as well.”
Turns out that all the lies and fraud that built Tesla’s grossly inflated valuation were related to a CEO who … wait for it … grossly spreads lies and fraud.
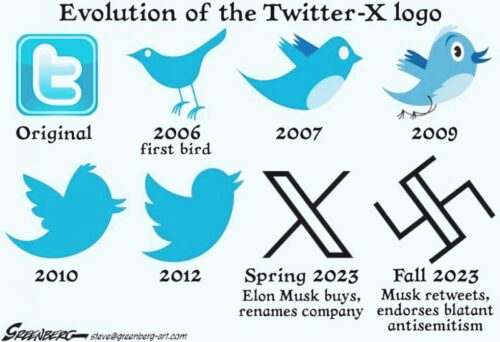
Swastika (formerly known as Twitter) is turning out exactly as I warned here back in April 2022.
Getting “pissed off” at Bernie Madoff or Lance Armstrong is a natural reaction, so it’s no surprise with this fraud either. But those guys at least didn’t spread such dangerous hate speech along with their scams.
The Tesla brand now is basically promoting harm as a hate symbol. That increasingly was the case ever since Elon Musk cruelly stole it from the founders. Now it is obvious.
People are starting to finally come to terms with their own role in supporting a hate platform.
For anyone who really wants to understand the American businessman to lunatic trajectory, please read the 1958 analysis of Henry Ford.
…can a genius be obtuse and even stupid? Can he be a man of uniformly limited ability, talent, and judgment? There is a mass of evidence, most if it uncontroverted, to show that Ford was all of these things. […] Nor would any man of political wisdom or even of ordinary political shrewdness have had truck with the Protocols of the Wise Men of Zion, a known forgery, or the rest of the racial rubbish that month after month appeared in the Dearborn Independent along with Ford’s own page and which blamed the Jews for virtually every misfortune ever experienced by man. When, in the end, the objection to this farrago became overpowering, Ford set a new standard for audacious falsehood by explaining that someone had put it all in the paper when he wasn’t looking. (Previously he had defended it as “eminently fair, temperate, and judicial.”)
Ford’s much-touted economic and social philosophy was a fraud.
Every Ford sold had a copy of the CEO’s unhinged anti-Semitic hate speech on the front seat packaged as “news”.
Adolf Hitler loved and admired Ford for such hate propaganda, in a similar way to the politicians who love and admire Musk today.

In other words if someone still says Ford or Musk deserve any respect they are either woefully ignorant of basic history, or a probable threat to democracy.



