The Washington Post has a well researched and written story about why the US Republican party is defined by their racism. Oh, maybe I should say spoiler alert:
…slavery’s enduring legacy is evident not only in statistics on black poverty and education. The institution continues to influence how white Southerners think and feel about race — and how they vote. Slavery still divides the American people
That’s right, the GOP uses racism to win, according to scientists who look at the data and patterns of voting. What they key in on is evidence that white children in racist families of the US south aren’t being educated away from their racism, and cling instead, which means racist sentiment will last many generations.
It is no coincidence that Jefferson Beauregard Sessions III, with his ties to the Klan in Georgia, was named Attorney General of the US in 2016 by the son of a Klansman.
In case it isn’t clear what that name represents…three generations of traitor-ship founded on racism:
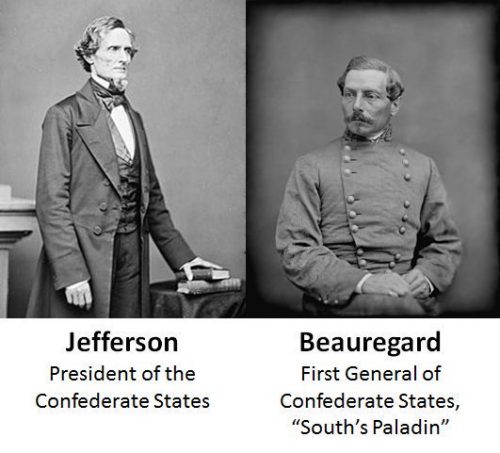
The question is who today would vote white supremacists into office to represent all people, given hateful statements and overt support from Klansmen. And the answer is clearly Republicans, using a signaling method called “personal responsibility” that denies slavery was a hardship, let alone requires restoration.
GOP doctrine on the importance of personal responsibility, together with elevated rates of black poverty and unemployment, help some Republicans rationalize their belief that people of color are inferior — beliefs they probably developed in childhood.
Today this is much easier to discuss than just eight years ago. Back then people were still trying to say Republicans had things to say that weren’t necessarily racist in foundation. Take for example this story from 2010:
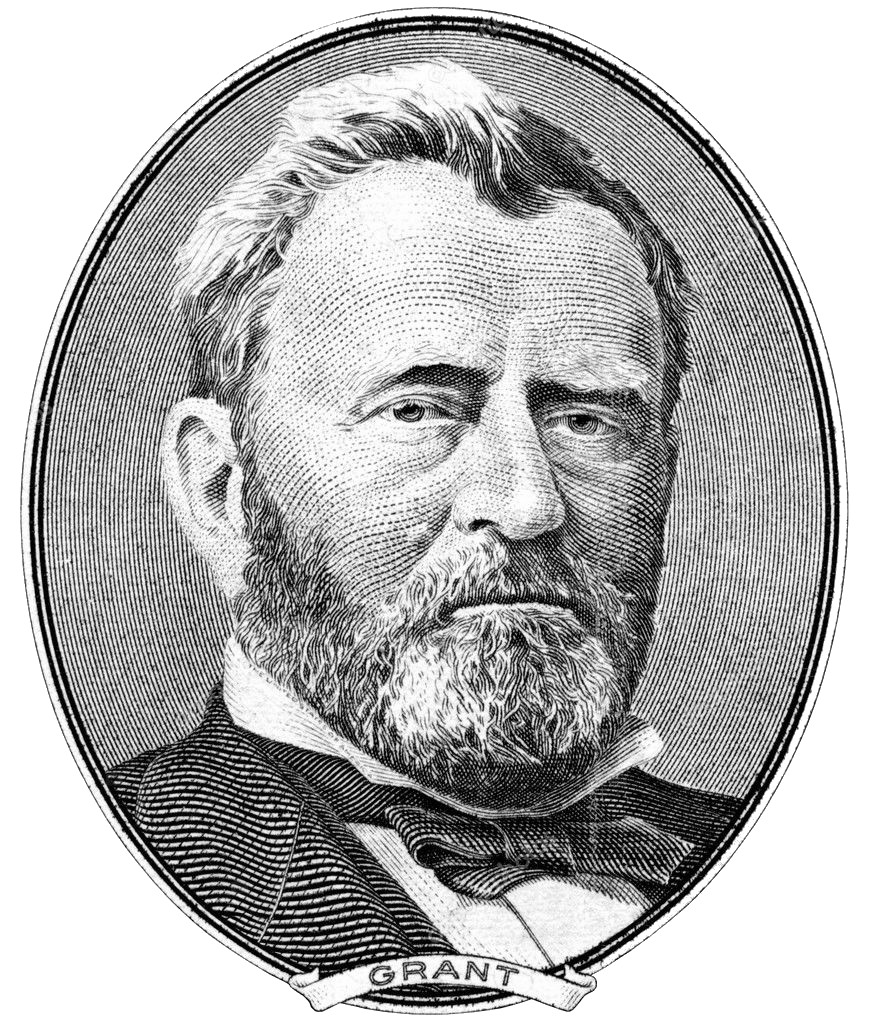
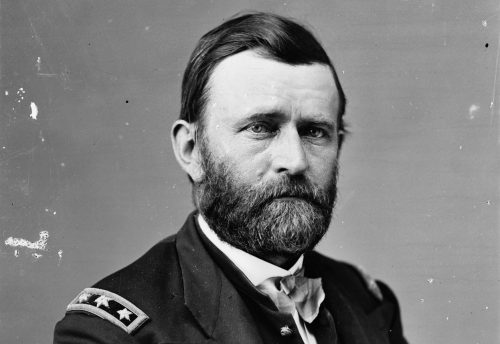
Shame on the 14 Republican congressmen who last week proposed substituting Ronald Reagan for Ulysses S. Grant on the $50 bill. Their action suggests they need a history lesson about the Northern general who won the Civil War and went on to lead the country.
That’s a great piece by a historian that doesn’t mention Republicans being racist.
To put this into context, a black president is elected in 2008. White Republicans then set about trying to remove President Grant from the $50 (despite being famous for being the greatest General in American history, one of the top three presidents in American history, and globally respected as a champion for human rights) and replace him with President Reagan, a man notorious for ties to white supremacists, campaigning on white supremacy, denigrating civil rights leaders like MLK (until he was forced to concede), and that’s not to mention supporting genocidal dictators. Here’s your Republican icon history right here:
Reagan chose [theme of violent white resistance to integration] to kick off his Deep South presidential campaign in 1980
Let’s look a little closer at the people trying to push Grant off the $50.
Rep. Patrick McHenry, R-N.C…introduced the legislation last month. He says it’s not about Grant but about honoring Reagan in the same fashion as Democratic presidents…
You have to marvel at the fact that McHenry doesn’t know that Grant was a Republican. Then you have to marvel at the fact McHenry is saying that pushing Grant off the bill isn’t about Grant. Do you think he meant that? Check out his own words, when he tried to explain:
…it has very little to do with Grant and so my response is very simple. I believe that Ronald Reagan, as most historians do, was the better president…
That means it absolutely is about Grant. McHenry is touting a white-supremacist line that Grant wasn’t a better president than Reagan. Grant won the civil war, introduced civil rights, created the DoJ, created the national parks, wrote an amazing autobiography in a race to finish before death from cancer…I mean his long list of accomplishments and massive popularity at his death should speak for themselves.
Reagan (perhaps most infamous for being absent minded, a figure-head and aloof while in office) has nothing on Grant, which we’re only talking about here because McHenry tried to argue Grant wasn’t better than Reagan, while saying it’s not about Grant. Reagan literally was almost removed by his own aides for being inept at his job, as they had to give him competency tests:
Most high-level White House aides believed that President Reagan was so depressed, inept and inattentive early last year in the wake of disclosures in November 1986 about the Iran-contra scandal that the possibility of invoking the 25th Amendment to remove him from office was raised in a memo to Howard H. Baker Jr., who was just taking office as Reagan’s chief of staff.
Former Baker aide James Cannon, confirming facts reported in a newly published book, said in an interview yesterday that he wrote a March 1, 1987, memorandum based on the aides’ concern and raising the possibility of applying the amendment.
Baker took the recommendation seriously and, with Cannon and two of his own aides, spent part of a day observing Reagan’s behavior before concluding that the president was sufficiently competent to perform his duties, according to the book.
Reagan is not a man who has any business threatening the amazing legacy of Grant, the warrior and patriot who reluctantly became president to continue to help save the nation and fight for freedom for all by destroying the KKK.
I combine the Washington Post story above with this one about their attempts to erase Grant from their own party to replace him with a barely competent Reagan who feted dictators and funded genocides… and it seems what the maps of the poor south really need is an infusion of Grant bills.
Send Grant back into the areas that are to this day being oppressed by the present-day Republicans who are perpetuating America’s racist legacy among their children and who refuse to end their family battle against civil rights.
Also let’s get Jackson off the $20 already…sheesh, talk about an awful legacy that should be deprecated ASAP.
“United States history is not Andrew Jackson vs. Harriet Tubman,” the Tennessee Republican said.
This week’s announcement that Jackson, a white slave owner from Tennessee, will be booted to the back of the $20 bill to make room for Tubman, a black anti-slavery activist, has left many in Jackson’s home state feeling that the change [will] diminish Jackson’s legacy [and] celebrate Tubman’s accomplishments.
That’s right. A Republican actually said US history is not about a white supremacist president who actively perpetuated slavery to expressly deny rights to black Americans, versus a black American who wanted rights.
That is so patently wrong. US history literally is about Jackson perpetuating slavery 30 years longer than the rest of the world. It is about all the moves he made from a white supremacist power position to block Tubman, and anyone else like her in the underdog reformer and freedom advocate seat, from being successful.
Time to send some Grant, send some Tubman, and tell the children in the US south all the real history of America that will help people be realists about how and why the Republican party is so racist.